📘 Executive Summary
The series: Over seven articles, we have traced the potential collapse of the free‑floating fiat system (1971–2026?), the rise of digital monetary blocs, and the emergence of the Network as a new Leviathan—a force as transformative as God in the 1800s and the State in the 1900s. The catalyst could be the Yuan Ultimatum: Iran’s demand that oil pass through the Strait of Hormuz only if priced in yuan, fracturing the 1974 petrodollar agreement. This could trigger a systemic collapse (The End of Free-Floating Fiat) as the debt supercycle and weaponization of finance end trust in state money.
The human stakes are laid bare in The Human Chokepoint: dissidents, refugees, and low‑score citizens may need privacy‑preserving digital cash to survive in a world of programmable exclusion. Intellectual validation came from the convergence of Sergei Glazyev and Ray Dalio (The Prophet and the Hedge Fund King): neutral assets must be unfreezable, private, decentralized, and fairly distributed.
When Institutions Fail mapped four scenarios—bloc implementation, state fracture, total collapse, and network state emergence—arguing that cryptocurrency could become the backup system when all else breaks. God, State, and Network introduced the three Leviathans and showed how secular and religious communities can encode their values into DAOs on Ryo.
This final article synthesises the series into a practical roadmap. It argues that Ryo Currency—with its forthcoming Halo 2 zero‑knowledge proofs, imminent high‑latency mixnet, proof‑of‑stake transition, and native DAO governance—is positioned to be the only cryptocurrency architected for every stage of the network state journey:
- Network union: a digital community with private treasury, ZK‑proof membership, and collective action.
- Network archipelago: crowdfunding physical nodes, smart‑property access, and private coordination.
- Network state: on‑chain census, unfreezable treasury, private governance, and diplomatic recognition via a bootstrap recognizer.
The article explores a full spectrum of governance models: pure free‑market DAOs (with Kleros arbitration), ideological DAOs (Communist, Corporate, Nationalist, Transhumanist, Anarcho‑Primitivist, Green), and religious DAOs (Hindu, Catholic, Islamic, Sikh, Buddhist, Jewish, Orthodox, Confucian)—each with its adherent count and existing institutional structures. It shows how an individual could belong to multiple DAOs simultaneously (e.g., a Kurdistan DAO, an Islamic DAO, a corporate DAO, and local micro‑DAOs) using the same Ryo wallet, with privacy preserved across all interactions.
The Recentralized Center is introduced as a vision of thousands of opt‑in network states, layered from foundation to community to affinity to local governance. Defense could shift from standing armies to cryptographic enforcement; policing might rely on smart contracts, arbitration, and local security DAOs; infrastructure could be sourced from legacy states or crowdfunded privately. Ryo is envisioned as the neutral settlement layer, enabling diverse polities to coexist and transact peacefully.
The verdict: The era of free‑floating fiat may be ending. The era of network states could be beginning. Ryo is designed to provide the missing piece: money that is private, sovereign, and governable by default. The path from network union to network state is open. The only question is who will walk it.
From Network Union to Network State: How Ryo Currency Powers the Digital Nations of Tomorrow
🚨JUST IN: UN officials have admitted the United Nations is on the brink of complete financial collapse because member states are refusing to pay their dues.
“We face a real danger of running out of money.”
This is freaking hilarious. Good!!Couldn’t happen to a more useless… pic.twitter.com/lrnjG9quu5
— Bethany O’Leary 🇺🇸 🦅 (@BBMagaMom) March 18, 2026
I. Introduction: The Vision Realized
Over the past week, we have traced the collapse of the free‑floating fiat system, the rise of digital blocs, and the emergence of the Network as the new Leviathan. In God, State, and Network, we examined how secular and religious communities alike can build DAOs on Ryo—private, fungible, and governable by default. Now we turn to the practical path: how a digital community becomes a sovereign network state, and why Ryo’s architecture makes it the ideal currency for every stage of that journey.
Balaji Srinivasan’s The Network State provides the roadmap. Ryo Currency provides the engine. This article explores how the two converge—how privacy‑preserving digital cash, fair distribution, and DAO‑native governance make Ryo the indispensable foundation for startup societies, from the first network union to the diplomatically recognized network state.
II. From Nation States to Network States: Srinivasan’s Framework
2.1 What Is a Network State?
Srinivasan defines a network state as “a highly aligned online community with a capacity for collective action that crowdfunds territory around the world and eventually gains diplomatic recognition from pre‑existing states” [2]. Its core components include a social network with a moral innovation, a sense of national consciousness, a recognized founder, an integrated cryptocurrency, an archipelago of crowdfunded physical territories, a virtual capital, and an on‑chain census that proves its scale [3].
2.2 The Network State System vs. The Nation State System
| Feature | Nation State System | Network State System |
|---|---|---|
| Primary | Physical first | Digital first |
| Territory | Contiguous land | Archipelago of crowdfunded properties |
| Citizenship | Birth‑based (jus sanguinis) | Consent‑based (opt‑in subscription) |
| Sovereignty | Military enforcement | Cryptographic enforcement |
| Governance | Paper laws, judiciary | Smart contracts, DAOs |
| Census | Every 10 years, paper‑based | Real‑time, on‑chain, verifiable |
| Money | Fiat currency (State‑controlled) | Cryptocurrency (Network‑native) |
The network state system assumes “digital first”—all nontrivial human‑created events start in the cloud and are then “printed” into the physical world [4]. Ryo’s architecture is built for this reality.
2.3 China vs. The Internet: A Framework for Understanding State Survival
Srinivasan draws a crucial distinction in understanding the future of nations: “Only China and crypto take the internet seriously, but in totally polar ways. They have the Great Firewall and the Blockchain respectively. These are very different types of fortifications that both treat the digital realm as something to be defended, walled off, and protected” [5]. China’s strategy is vertical integration of digital society—making citizens use only Chinese apps and restricting access to global platforms. This is digital sovereignty through control. Cryptocurrency’s strategy is horizontal—making software so secure it can run on every computer in the world, creating sovereignty through cryptography.
This framework raises a profound question: would a state like China be forced to enter the network state arena? The answer is that China is already creating its own version of a network state—but one built on surveillance, control, and the digital yuan rather than privacy, consent, and neutral money. The question is which model will prove more resilient when the old order collapses.
How would a reclusive, highly isolated state such as North Korea navigate the emergence of digital blocs and network states? The academic literature suggests that even economically strained regimes can survive through what scholars call “changing in order to stand still”—minimalist adaptation strategies that preserve core power structures [6]. North Korea’s extreme economic isolation and its parallel development of a domestic digital infrastructure (intranet, mobile payments, and a nascent cryptocurrency awareness) could, paradoxically, insulate it from the immediate shocks of fiat currency collapse. The regime might continue to function through barter, gold, and its own won while selectively engaging with digital bloc economies—for instance, through limited trade with China’s digital yuan sphere. Similarly, Turkmenistan, with its natural gas exports and tightly controlled economy, could navigate the transition by pegging its currency to a basket of digital assets or by striking bilateral deals with one of the emerging blocs. For both states, the emergence of network states does not necessarily imply collapse; it could instead create new opportunities for diplomatic and economic hedging—provided the ruling elites can manage the information flows and maintain domestic control. In a worst‑case scenario—a government collapse in Pyongyang—the humanitarian and security consequences would be severe (loose nuclear materials, refugee flows) [7], and network states could then emerge as lifeboats for populations left without institutions. But that is only one of several possible futures.
III. The Technology Stack: What Network States Need
3.1 Currency Requirements for Network States
- Unfreezable: No single state can seize the treasury (Glazyev’s requirement) [8].
- Private by default: Community economic activity must be invisible to rivals and hostile states (Dalio’s requirement) [9].
- Decentralized and uncapturable: No single point of failure; resistant to ASIC/botnet centralization [10].
- Fairly distributed: No insider class that can be coerced; no premine, no ICO, no venture capital control.
- Governable: Native support for on‑chain voting, treasury management, and DAO governance.
3.2 Why Existing Cryptocurrencies Fall Short
Not all cryptocurrencies are created equal. For a network state—a community that must survive in a world of hostile surveillance states, algorithmic enforcement, and financial warfare—the choice of monetary asset is existential. Here is why the most prominent cryptocurrencies fail to meet the requirements outlined above.
Bitcoin pioneered the concept of decentralized, censorship‑resistant money. But its transparency is a fatal flaw for network states. Every transaction is permanently visible on a public ledger. As Ray Dalio noted, Bitcoin “is not going to be a reserve currency for major countries because it can be tracked” [9]. Blockchain analytics firms have built multi‑billion dollar businesses tracing Bitcoin flows, linking addresses to identities, and flagging “tainted” coins [11]. For a dissident, this transparency can be deadly. For a religious community, it reveals who is donating to which causes, exposing believers to persecution. Furthermore, while Bitcoin began with CPU‑friendly mining, it has long since succumbed to ASIC domination. The majority of hash power is now concentrated in the hands of a few large manufacturers and mining pools, creating a centralization risk that violates the “decentralized and uncapturable” requirement. Bitcoin has no native governance mechanism—it changes through “rough consensus,” a process that is opaque and easily captured by entrenched interests.
Ethereum introduced smart contracts and programmability, but its ledger is equally transparent. Every DeFi transaction, every DAO vote, every treasury movement is visible to anyone with an internet connection. For a network state seeking privacy, this is unacceptable. Ethereum’s initial distribution was heavily concentrated through a premine and ICO, creating an insider class that can be—and has been—coerced by regulators. While Ethereum has transitioned to proof‑of‑stake, its validator set shows worrying trends toward centralization, with a few entities controlling a significant portion of staked ETH. Its governance remains off‑chain and opaque, subject to the same “core developer” dynamics that plague Bitcoin.
Zcash was the first major privacy cryptocurrency to deploy zero‑knowledge proofs, and it has resolved the trusted setup issue with its transition to Halo 2—the same next‑generation ZK‑proof technology that Ryo is adopting. Zcash offers users the choice between transparent and shielded transactions, and for many individuals and use cases, this optional privacy model provides exactly the right balance. A network state could, in principle, be built on Zcash. The key difference is one of design philosophy: Zcash’s privacy is optional, while Ryo’s is default. For a network state that requires absolute opacity—where the very fact of governance activity, treasury movements, or membership patterns must be hidden from adversaries—default privacy eliminates the signal that “something important is happening.” For communities that face existential threats from surveillance, Ryo’s architecture provides an additional layer of security. Both are viable; Ryo is for those who want to take privacy to the next level.
Monero is the dominant privacy cryptocurrency and has pioneered many important privacy technologies. Its upcoming FCMP++ (Full‑Chain Membership Proofs) upgrade represents a genuine advancement. However, Monero’s history and architecture present concerns for network states. Monero’s RandomX algorithm is designed for CPU mining, which in theory promotes decentralization. In practice, it has made Monero the preferred currency for cryptojacking—the unauthorized use of other people’s computers to mine cryptocurrency. As detailed in The Human Chokepoint, events like Operation EndGame and the Stary Dobry case highlight how botnet operators have mined millions of dollars worth of Monero using compromised devices [12]. A significant portion of Monero’s circulating supply has been mined by criminals, meaning that any network state using Monero would be transacting in coins with a history of criminal provenance.
More importantly, Monero remains on proof‑of‑work with no native governance layer. While its community is passionate, there is no on‑chain mechanism for voting on budgets, electing leaders, or managing a treasury. For a network state, this is a critical limitation. Monero could serve admirably as a base‑layer privacy tool for individuals, but for a community that must govern itself, make collective decisions, and manage a sovereign treasury, an asset with native DAO capabilities is essential. Ryo’s roadmap includes precisely this: a transition to proof‑of‑stake with integrated DAO governance, enabling network states to manage their affairs entirely on‑chain.
3.3 Ryo’s Architecture for Network States
- Privacy by default: Unlike Zcash’s optional privacy, Ryo’s Halo 2 ZK‑proofs make every transaction private—no signal, no two‑tier system [13]. For network states, this means adversaries cannot distinguish between treasury movements, governance votes, or ordinary transactions.
- Halo 2 zero‑knowledge proofs: Eliminate trusted setup, provide mathematically perfect privacy [14].
- High‑latency mixnet: Obfuscates network‑layer metadata—IP addresses, timing patterns, connection logs. Prevents traffic analysis even if on‑chain privacy is perfect [15].
- Cryptonight‑GPU mining: ASIC‑resistant, botnet‑resistant; ensures no single entity can dominate the network [16].
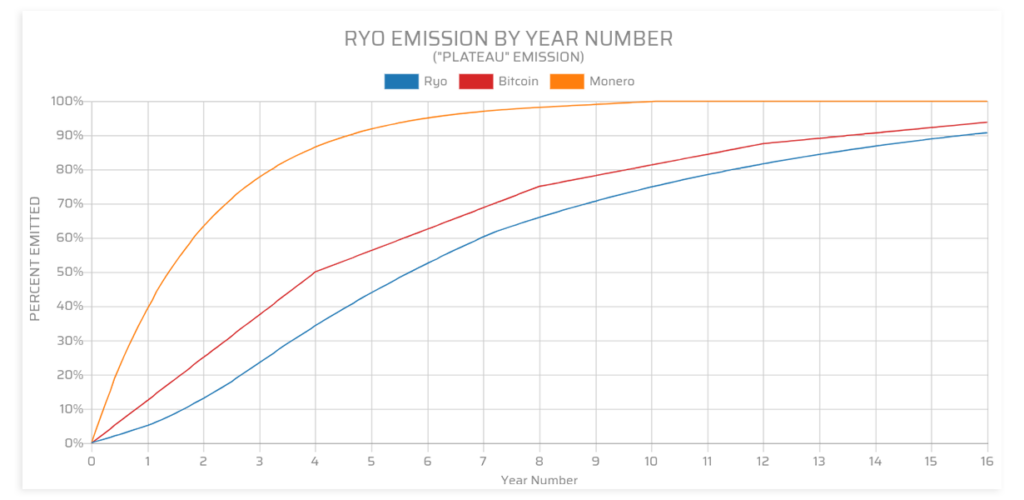
- Fair distribution: No premine, no ICO, 8.79 million pre‑mined coins burned at launch. No insider class that can be coerced [17].
- Proof‑of‑stake transition and DAO integration: Enables native on‑chain governance. Staking becomes the basis for citizenship, voting rights, and treasury management [18].
IV. The Network Union: Building Digital Community on Ryo
4.1 What Is a Network Union?
Srinivasan: “A social graph organized in a tree‑like structure with a leader, a purpose, a crypto‑based financial and messaging system, and a daily call‑to‑action” [19]. Unlike a social network, it has a purpose and engages in collective action.
4.2 How Ryo Powers the Network Union
- Private treasury: Union funds accumulate through member contributions; Ryo’s privacy hides treasury size and individual donations from adversaries.
- ZK‑proof membership: Members prove they belong without revealing identity—essential in hostile jurisdictions.
- Micro‑transactions for bounties: Reward contributions (writing, coding, organizing) with private, instant payments.
Example from God, State, and Network: Maria’s Catholic DAO uses Ryo for tithing, voting, and treasury allocation—all private, all on‑chain.
4.3 Public Displays of Alignment
Srinivasan’s concept: network unions must show the world they can coordinate [20]. Ryo enables transparent (to members) treasury management and private‑but‑verifiable collective actions—e.g., a keto‑kosher union crowdfunds a restaurant: the world sees that a restaurant was funded; only members see who funded it.
V. The Network Archipelago: Crowdfunding Physical Territory
5.1 What Is a Network Archipelago?
A network union that begins acquiring and networking physical properties around the world [21]. Properties are linked digitally; members move between nodes, creating a global diaspora of aligned individuals.
5.2 How Ryo Enables the Network Archipelago
- Cross‑border settlement: Members in different jurisdictions pool funds to acquire property. Ryo’s privacy hides the full extent of the archipelago from hostile states.
- Smart property access: Ryo‑based credentials unlock doors, access co‑working spaces, verify residency. The mixnet prevents correlation of access patterns.
- Proof‑of‑location: Future ZK‑proofs could allow members to prove they are in a node without revealing which node.
- Crowdfunding coordination: Ryo’s DAO tools enable transparent voting on acquisitions, budgets, and access.
Example: The Keto Kosher Archipelago—10,000 members crowdfund 50 apartments in 20 cities, each with keto‑friendly kitchens and gyms. Members book stays using Ryo; the DAO votes on new acquisitions and budgets.
VI. The Network State: Diplomatic Recognition and Sovereignty
6.1 What Is a Network State?
A network archipelago that gains diplomatic recognition from at least one legacy state [22]. Recognized as a legitimate polity; can issue passports, sign treaties, join international organizations.
6.2 How Ryo Supports the Network State
- On‑chain census: Ryo’s blockchain provides a real‑time, cryptographically verifiable census of citizens, income, and real‑estate footprint—the “proof of scale” needed for recognition [23].
- Unfreezable treasury: The state’s treasury is held in Ryo—no single state can freeze it (Glazyev’s requirement) [8].
- Private governance: Citizens vote on budgets, laws, and leaders using Ryo’s privacy features; no one can see how individuals voted, preventing coercion.
- Sovereign identity: Citizens hold Ryo‑based digital passports (e.g., via ENS). They can prove citizenship without revealing physical location.
6.3 The Bootstrap Recognizer
Srinivasan’s term for the first government to recognise a network state [24]. This initial recognition is the critical bridge between a digital community and the legacy international order—it provides legitimacy, access to physical territory, and a platform for further diplomatic relations.
Who might serve as a bootstrap recognizer? The most plausible candidates are small nations seeking economic diversification and a forward‑looking image. El Salvador’s recognition of Bitcoin as legal tender in 2021 is the archetypal precedent. Other examples could include:
- Small island nations (Tuvalu, Palau, Malta) that depend on digital services and could benefit from hosting network state headquarters.
- Special economic zones like the Dubai International Financial Centre or Hong Kong (before its absorption into China’s digital yuan system) that already operate under separate legal frameworks.
- Cities with crypto‑friendly mayors (Miami, Lugano, Zug) that could grant limited territorial recognition to network states within their boundaries.
- Indigenous nations with existing sovereignty claims, such as some Native American tribes, that could recognise network states as a form of economic development.
The recognition process would involve a bilateral agreement encoded in smart contracts. The bootstrap recognizer would grant the network state limited territorial jurisdiction (e.g., a plot of land for an embassy or a co‑working hub), diplomatic privileges, and legal recognition of its digital passports. In return, the network state would bring economic activity, technological expertise, and a share of its treasury (in Ryo) to the recognizer. The agreement would be self‑enforcing through smart contracts: if either party violates the terms, the contract automatically suspends privileges or redistributes funds.
For the bootstrap recognizer, the calculus is clear: a share of a growing digital economy far outweighs the modest territorial concession. For the network state, recognition unlocks a path to full sovereignty. As more recognizers emerge, network states can accumulate bilateral recognition, eventually gaining enough clout to join multilateral bodies or even the United Nations—if the UN still exists.
Example: The St. Therese Catholic Network State (500,000 members, $2 B annual income, properties in 30 countries) seeks recognition from Malta. Malta grants limited sovereignty—a digital embassy in Valletta, legal recognition of St. Therese passports, and a tax treaty. The network state’s treasury (in Ryo) remains unfreezable by any other state. Citizens now hold dual citizenship: Maltese (physical) and St. Therese (digital).
VII. The Digital Nation World Order: Governance Models for DAOs and Network States
7.1 The Collapse of the Old Order and the Survival of Religious Institutions
As documented in The Yuan Ultimatum and The End of Free-Floating Fiat, the 1971 monetary order is disintegrating. On March 18, 2026, UN officials admitted the organization is on the brink of complete financial collapse as member states refuse to pay their dues [1]. The institution created to maintain global order after World War II is now itself a casualty of that order’s dissolution.
If states themselves are fracturing—as explored in When Institutions Fail—and the multinational bodies they created are collapsing, what remains? The answer is networks. But also, perhaps, religious institutions.
History offers a powerful precedent. When the Roman Catholic Church lost its temporal power in the 19th century—its territories seized, its political authority shattered—it transformed rather than died. The creation of Vatican City in 1929 resolved a fundamental issue of papal sovereignty, giving the Church a tiny patch of earth from which to operate as a spiritual rather than temporal power. As Jonathan Laurence documents, facing the loss of executive powers, religious institutions “transformed their mission. They became beacons, advocates, and religious service providers for flocks outside their legal jurisdiction. This required ceding political-administrative control over the faithful. It also intensified the focus on performing spiritual oversight across jurisdictional borders by other means” [25].
This raises a crucial possibility: as the current nation-state order collapses, religious institutions—Catholicism, Islam, Orthodoxy, Sikhism, Buddhism, Hindu traditions—could survive and even gain power. They have millennia of experience with transnational organization, moral authority that transcends borders, and existing governance structures that could be ported directly into DAOs. In a world where the UN is bankrupt and states are collapsing, these religious networks could become the most powerful non-state actors. They could choose to become network states themselves—or they could become the moral compasses under which other network states operate.
7.2 The Spectrum of DAO Governance Models: Micro, Macro, and Network-State Level
DAOs operate at multiple scales, and understanding the differences is essential for network state design.
Micro‑governance DAOs are small, purpose‑bound communities—a guild of designers, a neighborhood association, a hobbyist club. They typically use simple token voting and off‑chain coordination. Their decisions affect only members, and disputes are often resolved socially. Examples from God, State, and Network include Maria’s Local Parent‑Teacher DAO and Neighborhood Watch DAO.
Macro‑governance DAOs are larger and more complex—DeFi protocols like Compound, Aave, or Morpho. These face what industry observers call a “midlife crisis”: the tension between decentralized ideals and commercial efficiency [26]. Some, like Compound, maintain pure on‑chain governance with long decision cycles (2‑4 weeks). Others, like Morpho, delegate market creation to professional curators, achieving rapid expansion (200 new markets in 2024) but risking curator centralization. Aave attempts a balancing act with dual‑track governance—DAO‑controlled main pools and KYC‑exclusive institutional markets. The tradeoffs are stark: decentralization brings security and legitimacy but slowness; delegation brings speed and efficiency but centralization risk.
Network‑state level governance DAOs are what this article concerns: DAOs that aspire to sovereignty. They must combine the legitimacy of macro‑governance DAOs with the agility of micro‑governance DAOs, plus additional layers: citizenship, territory, diplomacy, and defense. They require what Srinivasan calls “consensual government limited by a social smart contract”—a framework where members explicitly consent to be bound by the DAO’s rules, encoded in smart contracts, with the ability to exit at any time [27].
The key insight is that these levels are nested. A network state may contain within it thousands of micro‑governance DAOs (guilds, neighborhoods, affinity groups) and interface with macro‑governance DAOs (DeFi protocols, arbitration services). Ryo’s architecture supports all three levels through its privacy‑by‑default design and DAO‑native governance tools.
7.3 Pure Free Market DAOs and the Kleros Model
At the pure free market end of the spectrum are DAOs that impose no conditions beyond respect for property rights and voluntary exchange. They are platforms for economic cooperation, not moral communities. But even these require dispute resolution mechanisms. This is where Kleros enters.
Kleros is a blockchain‑based dispute resolution platform that relies on a network of jurors randomly selected from token‑holding users. Jurors evaluate submitted evidence and vote on outcomes, incentivized through a native token (PNK) [28]. It is, in the words of legal scholars, “a decentralized sheriff”—a socio‑legal organism where crowdsourced jurors, incentivized by game theory and cryptocurrency, attempt to fill the regulatory vacuum left by states.
The Kleros Governor contract allows DAOs to submit batches of transactions representing governance decisions. If multiple lists are submitted, a dispute is automatically created and jurors choose the correct list [29]. This creates a hybrid model: code‑fed substance wrapped in human judgment.
The critical question for network states is whether such rulings are enforceable. Under the New York Convention on the Recognition and Enforcement of Foreign Arbitral Awards, an award must be made in the territory of a contracting state to benefit from international enforcement. Stateless mechanisms risk falling outside this regime [28]. However, a 2021 Mexican court enforced a traditional arbitral award that embedded a Kleros decision, creating a procedural hybrid. This suggests a path forward: hybrid justice where decentralized rulings are reviewed by formal arbitrators, preserving enforceability while maintaining efficiency.
For pure free market DAOs, this is sufficient. They need only neutral arbitration for commercial disputes. They do not require shared morality—only shared consent to the rules of the platform.
7.4 Ideological DAOs: Political and Economic Doctrines
Communist DAO (Marxist Framework): Karl Marx’s Das Kapital (1867) provided a comprehensive critique of capitalism and a vision for a classless society organized around collective ownership of the means of production [30]. A DAO operating on Marxist principles would encode collective ownership through smart contracts, with voting power weighted by labor contribution rather than capital. The treasury would be managed democratically, and “profit” would be reinvested communally rather than distributed to stakeholders. Dispute resolution would prioritize restoration of collective harmony over punitive damages.
Here, Ryo’s privacy features enable a crucial innovation: a Communist DAO without the forced authoritarian compliance seen in historical communist states. Because membership is opt‑in and exit is always possible, there is no need for secret police, gulags, or show trials. The “dictatorship of the proletariat” becomes a voluntary association of consenting adults. Smart contracts enforce collective ownership, and Ryo’s privacy protects members from surveillance—including surveillance by their own DAO. This is communism without gulags, made possible by cryptography.
Corporate DAO Conglomerates: A different model entirely: DAOs structured as digital holding companies, with subsidiary DAOs operating as autonomous business units. These would be the successors to multinational corporations—but transparent, borderless, and governed by code rather than by opaque boards of directors. The governance structure would be weighted by stake, with voting rights proportional to investment or contribution. Disputes would be resolved through commercial arbitration, either traditional (via recognized arbitral institutions) or decentralized (via Kleros-style platforms).
The corporate DAO model offers several advantages over traditional corporate structures. First, it eliminates jurisdictional arbitrage—the practice of incorporating in tax havens to avoid regulation. The DAO exists on-chain, subject only to its own smart contracts and the arbitration agreements it enters into. Second, it enables fractional ownership of assets at unprecedented scale and liquidity. A corporate DAO could own real estate, intellectual property, or entire supply chains, with shares trading 24/7 on decentralized exchanges. Third, it solves the principal-agent problem that plagues traditional corporations: managers are replaced by smart contracts, and owners vote directly on major decisions.
However, corporate DAOs face significant challenges. How do they interact with legacy legal systems? Can they hold property, sign contracts, or defend themselves in court? The solution emerging is the “wrapped DAO”—a traditional legal entity (often a foundation or LLC) that holds off-chain assets and is controlled by the on-chain DAO. This hybrid model preserves the benefits of decentralized governance while maintaining legal personhood. As more jurisdictions pass DAO-friendly legislation (Wyoming’s DAO law, Malta’s blockchain framework), the need for such wrappers may diminish.
Nationalist DAOs: An ideology that cannot be ignored is nationalism—the belief that a particular nation or ethnic group should have its own sovereign polity. A Nationalist DAO would encode criteria for membership based on ancestry, language, or cultural affiliation. Voting power might be weighted by demonstrated commitment to the nation (e.g., living in the ancestral homeland, speaking the language, participating in cultural events). Dispute resolution would prioritize preservation of national identity and traditions. Such DAOs could become the digital expression of stateless nations—Kurds, Catalans, Tibetans—providing governance infrastructure for communities that lack territorial sovereignty.
Consider the Kurdish nation, spread across Turkey, Iran, Iraq, and Syria, with an estimated 30-40 million people but no state of their own [31]. A Kurdish DAO could unite the diaspora, crowdfund development projects in Kurdish regions, and provide educational and cultural services. It could issue digital identity credentials that prove Kurdish heritage without revealing location, protecting members from persecution. Over time, it could crowdfund physical nodes—cultural centers, schools, hospitals—in areas with high Kurdish concentration, creating a network archipelago. With sufficient scale (population, income, real estate), it could seek recognition from a bootstrap recognizer, gradually achieving the sovereignty that has eluded the Kurdish people for a century.
The Catalan nation offers a different model. With 7.5 million people and a clear territorial base in northeastern Spain, Catalonia already has many attributes of statehood—its own language, culture, parliament, and police force. A Catalan DAO could complement existing institutions, providing a parallel governance structure that transcends Spanish jurisdiction. It could manage Catalan-language education worldwide, fund research into Catalan history and culture, and coordinate the Catalan diaspora. In the event of a constitutional crisis in Spain, the DAO could serve as a shadow government, ready to assume sovereignty.
The Tibetan nation, with its unique Buddhist culture and history of theocracy, faces an even more challenging situation. Under Chinese control since 1950, Tibet’s population of 3.5 million has been subjected to cultural assimilation and demographic change. A Tibetan DAO could preserve Tibetan language and Buddhist teachings through digital archives, support monasteries in exile, and crowdfund development projects in Tibetan regions. It could issue digital passports to Tibetans worldwide, creating a recognized identity that the Chinese government cannot control. With sufficient scale, it could seek recognition as a government-in-exile, using network state mechanisms to achieve what traditional diplomacy has not.
Transhumanist DAOs: The transhumanist movement seeks to use technology to enhance human capabilities—extending lifespan, augmenting intelligence, merging with machines. A Transhumanist DAO would fund research into life extension, brain-computer interfaces, and artificial intelligence. Membership might require proof of contributions to these fields (via ZK-proofs to maintain privacy). Governance would be technocratic, with voting power weighted by scientific achievement rather than mere coin holdings.
The transhumanist vision is inherently global—it seeks to transcend not just national boundaries but biological ones. A Transhumanist DAO could fund the development of CRISPR therapies, cryonics facilities, and neural implant research. It could establish physical nodes near cutting-edge research institutions—the Salk Institute, MIT, Tsinghua University—where members could collaborate in person. Dispute resolution would prioritize scientific progress, recognizing that innovation requires tolerating failure and that ethical boundaries must be constantly renegotiated.
The implications for governance are profound. A Transhumanist DAO might weight voting by contributions to knowledge, not wealth. It might have mechanisms for “forking” when members disagree on the ethics of particular technologies. It might fund “longevity escape velocity” research with the explicit goal of achieving indefinite lifespans—a goal that transcends any single generation’s interests. Ryo’s privacy would protect members from discrimination based on their transhumanist beliefs, while its governance tools enable collective action on a global scale.
Anarcho-Primitivist DAOs: At the opposite extreme, anarcho-primitivists reject technology and advocate a return to pre-industrial ways of living. An Anarcho-Primitivist DAO would be paradoxical—using blockchain to fund off-grid communities, sustainable agriculture, and the preservation of traditional skills. Membership might require proof of living in a low-tech community, with heavy penalties for members who use banned technologies. Dispute resolution would follow traditional customs rather than coded rules.
Why would anarcho-primitivists use blockchain at all? Because even those who reject technology must interact with a world that uses it. A primitivist community needs to acquire land, defend its boundaries, and trade with outsiders. A DAO provides a way to do this without adopting the technological lifestyle internally. The DAO could hold title to communal land, manage a treasury of Ryo for purchasing supplies, and coordinate defense—all while members live off-grid, using only pre-industrial tools.
The paradox is productive. It reveals that even communities that reject technology can benefit from cryptographic governance. Ryo’s privacy ensures that their location and activities remain hidden from hostile outsiders. Its fungibility ensures that their coins are not tainted by association with the technological world. And its DAO tools enable them to govern themselves collectively, without hierarchy, in accordance with their values.
Green/Environmentalist DAOs: With climate change as a existential threat, Green DAOs could encode ecological principles into governance. Voting power might be weighted by carbon footprint (lower is better) or by contributions to environmental restoration. Treasuries would fund renewable energy, reforestation, and conservation projects. Dispute resolution would prioritize the rights of future generations and non-human species—a radical departure from anthropocentric legal systems.
7.4.6 A Note on Harmful Ideologies
Any honest survey of possible governance models must acknowledge that even abhorrent ideologies—violent religious extremism, ethno‑supremacism, terrorist organizations, and criminal enterprises—could in principle attempt to organize as DAOs. This is not an endorsement; it is an observation about the nature of consent‑based systems. The critical safeguard is that such a DAO could never impose itself on anyone. It would exist only through voluntary membership, and its ability to interact with the world would depend entirely on other DAOs choosing to recognize it. Foundation‑layer states could deny it access to infrastructure; neutral arbitration services could refuse to enforce its contracts; its members could be deplatformed from essential services; and physical‑world law enforcement would remain available in legacy states where its nodes are located. In a network state system, harmful ideologies are contained not by state violence but by the peaceful refusal of the wider community to cooperate with them. The paradox of tolerance is resolved through layered consent, not through censorship or coercion.
7.5 Religious DAOs: Ancient Wisdom Meets Digital Governance
Religious communities represent some of the largest and most resilient networks in human history. Their governance structures have evolved over millennia, and with over 5.8 billion adherents worldwide, they dwarf any state or corporation. Below we examine each tradition in depth.
Hinduism (Approx. 1.2 billion adherents): The ancient Hindu scriptures—the Vedas, Upanishads, Bhagavad Gita, Ramayana, Mahabharata, Artha Shastra, and Manu Smriti—encode sophisticated governance principles. As recent scholarship demonstrates, these texts contain frameworks for transparency, anti‑corruption, inclusive governance, and sustainable business that align with modern OECD guidelines [32]. Concepts such as Sama Darshana (equal vision), Vidya‑Dhana (knowledge as a gift), and Dharmic Governance offer a spiritually enriched foundation for ethical enterprise.
The Varna system, often misunderstood, is described in the Bhagavad Gita as a classification based on functional specialization—aptitudes for governing (Kshatriyas), commerce (Vaishyas), service (Shudras), and knowledge (Brahmins)—what Adam Smith would later call division of labor [33]. The Manusmriti even prescribes interest rates based on risk: Brahmins borrowing for yagnas pay the lowest rates, Kshatriyas funding conquests pay more, and Vaishyas financing overseas voyages pay the highest—a sophisticated recognition of risk premium thousands of years before modern finance.
A Hindu DAO could draw on this heritage. It might weight voting by demonstrated wisdom rather than mere coin holdings, structure governance to reflect functional specialization (separate councils for spiritual, commercial, and civic matters), and encode Dharmic principles of righteousness and duty into smart contracts. The Bhagavad Gita’s concept of swadharma—one’s own sense of right and wrong—becomes a personalized moral compass within a collectively governed framework. Dispute resolution could involve panels of respected gurus or acharyas, with rulings enforced on-chain.
Catholicism (Approx. 1.3 billion adherents): The Catholic Church possesses the most sophisticated hierarchical governance structure in human history, centered on the Vatican and the papacy. The Pope, as the successor of Peter, holds supreme legislative, executive, and judicial authority. The Roman Curia, the College of Cardinals, and the Synod of Bishops provide advisory and administrative support. Canon law, a comprehensive legal system dating back centuries, governs everything from sacraments to property disputes.
A Catholic DAO could integrate with this existing framework in multiple ways. At minimum, it could encode Catholic moral teaching (e.g., Mensuram Bonam investment guidelines) into its smart contracts [34]. More ambitiously, it could create a parallel digital structure that recognizes the Pope as ultimate arbiter of moral questions, while handling day‑to‑day governance through on‑chain voting. Disputes involving doctrine could be referred to Vatican authorities; commercial disputes could be settled through the DAO’s own arbitration mechanisms.
The Church’s global diocesan structure could become a network archipelago, with parishes as nodes and the Vatican as the virtual capital. Tithes could flow automatically through smart contracts, with privacy preserved for donors. Bishops could be elected by local DAOs, with their authority recognized by the central Church DAO. As Laurence notes, the Church survived its loss of temporal power by transforming its mission: it became “beacons, advocates, and religious service providers” operating across jurisdictional borders [25]. A Catholic DAO is the logical extension of this evolution—a digital diocese for the network state era.
Islam (Approx. 1.9 billion adherents): Islamic governance has historically combined religious authority (ulema) with political authority (caliphate). The Ottoman caliphate, in its final century, flourished as a spiritual project, abandoning efforts to reclaim lost lands and pursuing spiritual dominion instead—a precedent for religious authority without temporal power [25]. Sharia law provides a comprehensive framework for personal conduct, commerce, and governance, with different schools of jurisprudence (Hanafi, Maliki, Shafi’i, Hanbali, Ja’fari) offering varied interpretations.
A Sharia‑compliant DAO would encode prohibitions on riba (interest) and requirements for risk‑sharing directly into its smart contracts [35]. All financial transactions would be asset‑backed, with speculation prohibited. For dispute resolution, the DAO could establish a digital shura (council) of qualified scholars, whose rulings would be enforced on‑chain. Different schools of Islamic jurisprudence could give rise to competing DAOs, each encoding its own interpretation of Sharia—much as different Protestant denominations emerged from the Reformation.
The global Muslim community (ummah) already functions as a transnational network, with the Hajj pilgrimage as the ultimate public display of alignment. A Muslim network state could build on this foundation, with mosques as nodes, the Kaaba as a virtual capital, and the principles of zakat (obligatory alms) automated through smart contracts. Ryo’s privacy would protect donors and recipients alike, fulfilling the Quranic ideal of charity given without expectation of reward.
Sikhism (Approx. 25-30 million adherents): The Sikh tradition has existing institutional structures that could integrate with DAOs. The Akal Takht (the highest temporal seat of authority) and the Shiromani Gurdwara Parbandhak Committee (SGPC) provide established governance frameworks [36]. The Guru Granth Sahib serves as the eternal Guru, and congregational decision-making (sangat) has deep roots in Sikh practice. The Sikh Rehat Maryada (Code of Conduct) provides detailed rules for communal life and dispute resolution [37].
A Sikh DAO could encode the three pillars of Sikhism into its governance: Kirat Karo (honest labor) through a reputation system that verifies fair dealing, Vand Chhako (sharing) through automated tithing to community funds, and Naam Japo (meditation) through community‑funded gurdwaras and meditation centers. The langar tradition of free community meals could be funded through a dedicated treasury, with Ryo’s privacy ensuring that donors remain anonymous.
Disputes could be referred to a digital sangat (congregation), with serious matters escalated to a panel of respected granthis whose rulings would be enforced on‑chain. The Akal Takht could serve as the ultimate appellate authority, with its edicts automatically executed across the network state’s jurisdiction. As with other traditions, Ryo’s privacy would protect members from surveillance while maintaining accountability through transparent treasuries.
Buddhism (Approx. 500 million adherents): Buddhist governance varies significantly across traditions, but the Dalai Lama’s leadership of Tibetan Buddhism provides one possible model. The Sangha (monastic community) has centuries of experience with collective decision-making, often through councils of senior monks. The Vinaya Pitaka, part of the Pali Canon, provides detailed rules for conduct and dispute resolution [38]. The Foundation for the Preservation of the Mahayana Tradition (FPMT) offers a contemporary example of a global Buddhist organization with centralized guidance and local autonomy [39].
A Buddhist DAO would encode the principle of right livelihood, prohibiting investments in weapons, intoxicants, or businesses that cause suffering. The treasury would fund meditation centers, monasteries, and educational institutions. Governance could be structured around a council of respected teachers, with voting weighted by demonstrated wisdom and compassion rather than mere coin holdings.
Dispute resolution would emphasize the restoration of harmony over punitive measures. The Vinaya’s procedures for addressing transgressions—confession, restitution, and, in serious cases, expulsion—could be encoded in smart contracts. Ryo’s privacy would protect the identities of those seeking guidance or confession, while ensuring that serious matters are addressed by the community.
Judaism (Approx. 15 million adherents): Jewish communities have millennia of experience with self‑governance in diaspora. The beit din (rabbinical court) system provides a sophisticated framework for dispute resolution, with a hierarchy of local, regional, and central courts. The Talmud contains extensive commercial law, including detailed regulations on partnerships, loans, and property [40]. Modern organizations such as the Rabbinical Council of America provide models for transnational religious governance [41].
A Jewish DAO could draw on this tradition, with a digital beit din for dispute resolution, tzedakah (charity) obligations automated through smart contracts, and heter iska (partnership agreements) encoded for business transactions. The DAO could recognize the authority of existing rabbinical bodies while handling day‑to‑day governance on‑chain. The concept of dina d’malkhuta dina (“the law of the land is law”) would guide interactions with other network states, providing a framework for recognizing external jurisdiction when appropriate.
Ryo’s privacy would protect donors to tzedakah funds, fulfilling the highest form of charity (where neither giver nor receiver knows the other). The mixnet would prevent surveillance of Jewish communities, a critical protection given centuries of persecution. The DAO could also fund physical security for synagogues and community centers, with allocations transparent to members but hidden from adversaries.
Orthodox Christianity (Approx. 220 million adherents): The Orthodox Church’s conciliar governance—councils of bishops making decisions collectively—maps naturally to DAO structures. The Ecumenical Patriarch holds a primacy of honor rather than jurisdiction, with each autocephalous church governing its own affairs. This decentralized model aligns with network state principles.
A Philanthropia Treasury could fund charitable works, with contributions private but distributions publicly auditable. The principle of oikonomia (economy, or dispensation) would allow for flexible application of canonical rules in individual cases, handled through private ZK‑proof submissions to a council of spiritual elders [42]. The DAO could support monasteries as physical nodes in the network archipelago, with monks providing spiritual guidance and the DAO providing material support.
Dispute resolution would involve councils of bishops or respected elders, with rulings enforced on‑chain. The conciliar model ensures that no single bishop can dominate, while Ryo’s privacy protects individual bishops from political pressure. The Orthodox tradition’s emphasis on beauty and liturgy could also fund digital iconography and virtual worship spaces.
Confucianism (Ethical framework for approx. 1.5 billion people in East Asia): While not a religion in the Western sense, Confucianism provides a comprehensive ethical framework that has governed East Asian societies for millennia. The Analects, Mencius, and other classics emphasize ren (benevolence), yi (righteousness), li (ritual propriety), and zhi (wisdom).
A Confucian DAO would prioritize yi (righteousness) over li (profit), weight voting by demonstrated virtue, and structure governance to mirror the five key relationships [43]. Dispute resolution would emphasize harmony and the restoration of relationships, guided by the judgment of a council of elders. The concept of the “junzi” (exemplary person) could serve as a model for leadership, with leaders chosen for their moral character rather than their wealth.
Ryo’s privacy would protect individuals from surveillance while allowing the community to recognize virtuous conduct through ZK‑proofs. The DAO could fund educational institutions, ancestral rites, and community welfare programs. In a world where the nation-state order is collapsing, Confucian principles could provide a stable foundation for governance, drawing on millennia of experience with managing complex societies without centralized coercion.
7.6 Living in Multiple DAOs: The Kurdistan Example
How would an individual navigate this complex landscape of overlapping DAOs? Consider a Kurdish Muslim woman, Ayla, who lives in a secular foundation state (e.g., the Austin Free Market Network State) but participates in multiple communities:
- Kurdistan DAO: Ayla proves her Kurdish heritage through ZK-proofs, gaining access to cultural education, language preservation projects, and a diaspora mutual aid network. She votes on funding for schools in Kurdish regions and contributes to a treasury that supports Kurdish political advocacy.
- Islamic DAO: Ayla participates in a Sharia‑compliant DAO for her religious community. Her zakat obligations are automatically calculated and distributed, with privacy preserved. The DAO funds local mosques and provides halal investment opportunities.
- Multinational Corporate DAO: Ayla works as a software engineer for a corporate DAO that operates globally. Her salary is paid in Ryo, and she holds governance tokens that give her a voice in company decisions. The DAO’s smart contracts handle payroll, benefits, and dispute resolution without revealing her identity to colleagues.
- Micro‑DAOs: Ayla belongs to a neighborhood watch DAO that coordinates security in her physical community, a professional guild for software engineers, and a hobbyist DAO for traditional Kurdish weaving. Each uses Ryo for micro‑transactions and ZK‑proofs for membership verification.
All of these memberships are managed through the same Ryo wallet, with privacy preserved across all interactions. No single DAO can see her activities in others. This is the power of the network state system: individuals can participate in multiple communities, each governing different aspects of their lives, without surveillance or coercion.
7.7 Dispute Settlement in a World of Diverse DAOs
When DAOs with radically different governance models interact—a Catholic DAO contracting with a Communist DAO—how are disputes resolved? The answer is the same as in international trade today: through agreed‑upon arbitration mechanisms.
Two DAOs entering into a contract would specify in advance the dispute resolution procedure. This could be:
- Neutral arbitration: A decentralized service like Kleros, where jurors are selected randomly and rulings enforced automatically by smart contracts.
- Religious arbitration: Both parties agree to submit disputes to a specified religious authority, whose rulings are encoded on‑chain.
- Hybrid arbitration: A multi‑stage process, with initial attempts at mediation within each DAO’s framework, escalating to neutral arbitration if necessary. The Mexican precedent—a Kleros decision wrapped in a formal arbitral award—provides a model for such hybrids [28].
The key insight is that technology does not eliminate diversity; it enables diverse communities to coexist peacefully by providing neutral infrastructure for interaction when they choose to interact, and allowing complete separation when they prefer.
VIII. Defense, Policing, and Infrastructure in the Network State Era
8.1 The Problem of Violence
Any polity that aspires to sovereignty must address the fundamental challenge of violence—both external (defense) and internal (policing). In the network state era, these functions will look very different than in the nation-state system.
External defense relies less on standing armies and more on what Srinivasan calls “cryptographic enforcement” [4]. A network state’s treasury is unfreezable, its communications are encrypted, and its members are distributed across jurisdictions. Attacking such a state is not like invading a territory; it is like trying to arrest a cloud. The 2022 freezing of Russian assets demonstrated that physical states can be attacked financially, but a network state with assets in Ryo is immune to such measures.
Internal policing is more complex. How does a network state handle violent crime, theft, or fraud? The answer lies in a layered approach:
- Smart contract enforcement: Many crimes can be prevented through code. Theft is impossible without private keys. Fraud requires falsifying ZK-proofs, which is computationally infeasible.
- Decentralized arbitration: For disputes that cannot be prevented, Kleros-style arbitration provides resolution without physical force.
- Local security DAOs: Physical nodes of the network archipelago would have their own security arrangements—neighborhood watch DAOs, private security contracts, or agreements with local police.
- Reputation systems: Members who violate norms lose access to network state services, a powerful deterrent.
For serious violent crime, network states would likely contract with existing law enforcement agencies. A Catholic network state in Malta would rely on Maltese police to investigate murder, just as a foreign embassy relies on host-country law enforcement today. Over time, network states might develop their own security forces, but only after achieving sufficient scale and territorial concentration.
8.2 Real-World Infrastructure: Roads, Bridges, Power
Infrastructure presents a different challenge. Network states are archipelagos, not contiguous territories—they cannot build a single highway system spanning their nodes. Instead, they rely on the infrastructure of the legacy states in which their nodes are located.
This is not as limiting as it sounds. Even today, most infrastructure is provided by local governments. A network state’s nodes would be located in cities and towns that already have roads, utilities, and emergency services. The network state pays for these services through taxes or fees to the local jurisdiction, just as any resident or business does.
For infrastructure that network states need but cannot source locally—such as private high‑speed internet links between nodes—they can crowdfund and build it themselves. This is already happening with Starlink and community mesh networks. Ryo’s treasury tools enable transparent funding and governance of such projects.
IX. The Recentralized Center: A World of Network States
9.1 What Is the Recentralized Center?
Srinivasan’s answer to both American Anarchy and Chinese Control [44]. It is not a return to the nation-state system, but a new form of political organization that combines the best of both worlds: the flexibility and consent of decentralized networks with the stability and coordination of centralized governance.
The recentralized center is a world of many network states, each with its own moral code, all connected through neutral protocols. It is conscious recentralization into opt‑in communities—not imposed from above, but built from below by people who choose to associate with each other. It is the opposite of both anarchy (no governance) and tyranny (imposed governance).
In practice, the recentralized center would function through a nested hierarchy of DAOs:
- Foundation layer: Secular, neutral network states that provide basic infrastructure—property rights, dispute resolution, physical security—to anyone who opts in. These are the digital equivalent of international waters: platforms for cooperation without moral content.
- Community layer: Religious and ideological DAOs that provide shared values, mutual aid, and worship. Members of these DAOs also belong to foundation-layer states, which handle matters on which all can agree.
- Affinity layer: Single-issue DAOs for hobbies, professions, or causes. These cut across community lines, enabling cooperation on specific projects without requiring agreement on deeper values.
- Local layer: Physical proximity DAOs for neighborhoods, towns, and cities. These handle matters that require geographic coordination—roads, utilities, emergency services—while respecting the diverse values of their members.
This layered model ensures that individuals are never forced to choose between their values and their livelihoods. A Catholic can live in a secular foundation state, worship in a Catholic DAO, work in a professional guild, and participate in a neighborhood watch—all using the same Ryo wallet, all protected by the same privacy layer, all governed by the same cryptographic guarantees.
9.2 How the Recentralized Center Differs from the Nation-State System
The recentralized center is not simply the nation-state system reborn. The differences are fundamental:
| Aspect | Nation-State System | Recentralized Center |
|---|---|---|
| Membership | Birth‑based, involuntary | Consent‑based, opt‑in |
| Governance | Territorial, top‑down | Functional, layered, bottom‑up |
| Dispute resolution | Courts, coercion | Arbitration, exit |
| Identity | Single, exclusive | Multiple, nested |
| Money | State‑controlled fiat | Neutral cryptocurrency (Ryo) |
| Legitimacy | Elections, force | Consent, cryptography |
The recentralized center thus resolves the ancient tension between individual freedom and collective action. Individuals are free to choose which communities to join, and communities are free to govern themselves according to their values—but all are bound by the neutral infrastructure that enables them to interact peacefully.
9.3 Ryo as the Neutral Settlement Layer
Just as gold served Catholic monarchies, Protestant merchants, and Islamic caliphates, Ryo can serve diverse network states. A Catholic state and a secular libertarian state can transact using Ryo—neutral, private, uncensorable. The mixnet can even hide the fact of transaction between states, preventing adversaries from mapping the network state system.
Ryo’s privacy features are essential here. In a world where many states may be hostile to each other, the ability to transact privately prevents adversaries from targeting specific communities. A Catholic state trading with a Muslim state should not have its transactions visible to a hostile third party. Ryo’s default privacy ensures that such transactions remain confidential, while its DAO governance tools enable states to manage their own internal affairs.
9.4 Interoperability and the Network State System
Multiple network states can recognize each other’s citizens and passports through bilateral agreements encoded in smart contracts. A citizen of the Catholic network state traveling to the Sikh network state could present a ZK‑proof of their citizenship, revealing nothing else about themselves. The two states could agree to enforce each other’s civil judgments, creating a web of reciprocal recognition.
Future developments could include atomic swaps between network state currencies, all settled in Ryo. A citizen of the Communist DAO could exchange labor credits for goods from the Corporate DAO, with the swap executed automatically and privately. The recentralized center thus enables a global economy that respects local values.
9.5 The Vision: A Multipolar World of Digital Nations
Thousands of network states, populations from 10,000 to 10 million. Citizens hold multiple citizenships, participate in multiple DAOs, and move freely between physical nodes. Ryo is the common economic layer—private, fungible, governable. As Srinivasan writes: “The network is the lives (national network), the land (metaverse subnet), the law (governance network), and the Leviathan (Bitcoin network) all packed into one” [45]. For network states, Ryo fulfills all four roles.
This vision is not a fantasy. The technology exists. Ryo provides the missing piece: money that is private, sovereign, and architected for the network age. The path from network union to network state is open. The only question is who will walk it.
X. Conclusion: The Architecture of Freedom
We began this series with a missile‑strike on the Strait of Hormuz and end with a vision of thousands of digital nations. The old system—free‑floating fiat, unipolar hegemony, the UN itself—is dying. The new system—digital blocs, programmable money, algorithmic surveillance—is being born. But within that system, a third force has emerged: the Network Leviathan.
Ryo Currency is not just another privacy coin. It is the economic layer for the network state era. It meets every requirement that thinkers from Glazyev to Dalio to Srinivasan have identified: unfreezable, private, decentralized, fairly distributed, governable. It supports communities at every stage, from the first network union to the diplomatically recognized network state. While Ryo’s current liquidity and market cap are still growing, its technical roadmap is explicitly designed for exactly this use case.
Srinivasan’s roadmap is not a fantasy. The technology exists. Ryo provides the missing piece: money that is private, sovereign, and architected for the network age. The path from network union to network state is open. The only question is who will walk it.
As Adam Smith understood, markets require a moral foundation. In the network state era, that foundation is not imposed by a sovereign—it is chosen by each community, encoded in its DAO, and protected by cryptography. Ryo is the neutral substrate that enables this diversity to flourish.
In the age of the Network, sovereignty is no longer granted. It is compiled.
The era of free‑floating fiat is over. The era of network states has begun. The only question is whether you will have the tools to move between them.
XI. Call to Action
- Read Balaji Srinivasan’s The Network State. Understand the full framework.
- Study Ryo’s roadmap: Halo 2, mixnet, proof‑of‑stake, DAO integration.
- Join or start a network union. Use Ryo to organize, transact, and govern.
- Prepare for the next stage: crowdfunding territory and building the network archipelago.
- Share this series. The more people understand what’s coming, the better prepared we all will be.
References & Further Reading
- [1] Bethany O’Leary on X: UN financial collapse, Mar 18, 2026
- [2] Srinivasan, Balaji. The Network State: Chapter 5, Section 5.3.1 “What is a Network State?”
- [3] Ibid., Chapter 5, Section 5.3.1 (definition breakdown)
- [4] Ibid., Chapter 5, Section 5.3.2 “What is the Network State System?”
- [5] CoinMarketCap Academy: “Balaji Srinivasan on China vs. Crypto”
- [6] “CHANGING IN ORDER TO STAND STILL: THE CASE OF SURVIVALIST NORTH KOREA.” KCI.
- [7] “Planning for North Korean Collapse: Military Missions and Requirements.” KCI.
- [8] Escobar, Pepe. “How the BRICS+ Unit Project Can Dethrone the Dollar.” Yerepouni Daily News, Nov 2025.
- [9] Hanke, Steve. “Ray Dalio on Bitcoin.” X, Nov 22, 2025.
- [10] Srinivasan, Balaji. The Network State: Chapter 2, Section 2.4 “God, State, Network”
- [11] Gate.com: Privacy Coins Analysis
- [12] Ryo News: The Human Chokepoint
- [13] Ryo News: How Ryo Currency is Redefining Privacy
- [14] Halo 2 Documentation
- [15] Cypherphunks: Mix Networks
- [16] Bitget Wiki: What is Ryo Currency?
- [17] Ryo Currency GitHub Repository
- [18] Ryo Currency FAQ4 – Roadmap
- [19] Srinivasan, Balaji. The Network State: Chapter 5, Section 5.3.8
- [20] Ibid.
- [21] Ibid.
- [22] Ibid., Chapter 5, Section 5.3.1
- [23] Ibid.
- [24] Srinivasan, Balaji. The Network State: Chapter 5, Section 5.3.8
- [25] Laurence, Jonathan. “Out of Office: Rejoining Civil Society.” Princeton University Press. Project MUSE
- [26] “Governance Innovation of On-Chain Credit Infrastructure.” ChainCatcher, 2025.
- [27] Srinivasan, Balaji. The Network State: Chapter 5, Section 5.3.1
- [28] “Decentralised Justice and the New York Convention.” Wolters Kluwer, 2025.
- [29] “Kleros Governor Documentation.” Kleros.
- [30] Marx, Karl. Das Kapital, 1867. Marxists Internet Archive
- [31] BBC News: “Who are the Kurds?”
- [32] Vijayasimha, Narendra. “Ancient Indian Wisdom and the OECD Guidelines: A Cross-Civilizational Dialogue on Responsible Business Conduct.” Nepal Journals Online, 2025.
- [33] “Varna system is misunderstood: Bibek Debroy.” Times of India, 2018.
- [34] Archdiocese of San Antonio: How should Catholics manage their money
- [35] Visser, Hans. “Islamic Finance: Principles and Practice.” Edward Elgar Publishing, 2013. Publisher Link
- [36] Shiromani Gurdwara Parbandhak Committee (SGPC) Official Website
- [37] Sikh Coalition: Sikh Rehat Maryada (Code of Conduct)
- [38] Access to Insight: Vinaya Pitaka (The Monastic Code)
- [39] Foundation for the Preservation of the Mahayana Tradition (FPMT)
- [40] Sefaria: The Talmud
- [41] Rabbinical Council of America
- [42] Greek Orthodox Archdiocese: The Orthodox Christian Understanding of Economics
- [43] Rajapaksha, et al. “Balancing Profit and Morality: Confucian Insights into Financial Management.” Vidyodaya Journal, 2024.
- [44] Srinivasan, Balaji. The Network State: Chapter 4, Section 4.7 “Towards a Recentralized Center”
- [45] Ibid., Chapter 5, Section 5.3.3 “The Network State as a Term”
This article is the seventh in an ongoing series. Read the first: The Yuan Ultimatum. Read the second: The End of Free-Floating Fiat. Read the third: The Human Chokepoint. Read the fourth: The Prophet and the Hedge Fund King. Read the fifth: When Institutions Fail. Read the sixth: God, State, and Network.