📘 Executive Summary
On April 1, 2026, Iran reopened the Strait of Hormuz—but only for ships paying tolls in Chinese yuan or cryptocurrency. At the same time, the Iranian rial is collapsing: a new 10 million banknote is worth less than $7, and inflation is nearing 50%. This is the culmination of the Yuan Ultimatum we traced in our first series. In this moment of crisis, the choice of cryptocurrency is not trivial. Regulated stablecoins like USDT and USDC are not neutral; they are freezeable extensions of the dollar system. This article argues that one of the few architectures aligned with true monetary sovereignty is Ryo Currency—a privacy coin designed with default privacy, unfreezability, fair distribution, and future DAO‑native governance. Drawing on the neutral money doctrine developed by Sergei Glazyev, Ray Dalio, and Balaji Srinivasan, we demonstrate why such properties matter for any nation seeking to escape the bloc system.
Strait of Crypto: Iran, the 10 Million Rial Note, and the Search for a Sanction‑Proof Asset
[1]. This is the moment we predicted in The Yuan Ultimatum: the petrodollar’s chokehold on global energy trade has been broken, replaced by a multipolar system of competing currencies.
I. Introduction: The Watershed Moment
On March 14, 2026, Iran closed the Strait of Hormuz. Twenty percent of the world’s oil stopped moving. Warships gathered. Missiles struck. The world held its breath. Today, the Strait has reopened—but not on the terms the United States demanded. According to Bloomberg, Iran is now accepting toll payments in Chinese yuan and cryptocurrency, with the Islamic Revolutionary Guard Corps operating a dedicated payment desk at Bandar Abbas [1]. This is not a diplomatic compromise. It is a financial coup.
The timing is no coincidence. As Martin Armstrong noted just days before, Iran introduced a 10 million rial banknote—the highest denomination in the country’s history—worth less than $7 at open market rates [2]. The rial has lost tens of thousands of times its value since 1979. Inflation is approaching 50%. The currency is functionally dead. When a government prints million‑denomination notes just to keep commerce functioning, it is admitting that its money has failed.
🚨 IRAN JUST PRINTED A 10 MILLION RIAL BANKNOTE — ANOTHER PAPER CURRENCY DYING IN REAL TIME! 🚨
Iran’s central bank just issued the largest denomination note in its history as inflation spirals out of control from war, sanctions, and endless money printing. History is repeating itself.
But what cryptocurrency is Iran accepting? The Bloomberg report mentions “cryptocurrency” without specifying. Some analysts have speculated that Iran is accepting stablecoins like USDT or USDC—a suggestion that reveals a profound misunderstanding of what “neutral money” actually requires. As we explored throughout the seven‑article series, regulated stablecoins are not neutral. They are freezeable, surveilled, and ultimately subject to the same dollar system that Iran is trying to escape.
This article argues that one of the few architectures aligned with true monetary sovereignty is a privacy coin—and that among privacy coins, Ryo Currency is designed to meet the requirements of the network state era: private by default, unfreezable, fairly distributed, and governable by its community. The Strait of Hormuz has reopened. The question now is whether the world will recognize the kind of money that can actually pass through it.
II. The Rial Collapse: A Textbook Monetary Breakdown
To understand why Iran is turning to cryptocurrency, we must first understand the scale of the monetary collapse it is trying to escape. The rial’s trajectory is a case study in the death of fiat currency.
At the time of the 1979 revolution, the exchange rate was roughly 70 rials per dollar. Today, on the open market, it trades at 1.4 to 1.6 million per dollar—a loss of tens of thousands of times its value [2]. Even in the past year alone, the decline has accelerated. Official inflation figures hover near 50%, with food prices rising even faster. As Armstrong writes, “When a nation must print larger and larger notes just to keep commerce functioning, that is not stability, it is a monetary breakdown.”
The introduction of a 10 million rial banknote—now the highest denomination in the country’s history—is the final signal. Governments in Weimar Germany and Zimbabwe followed the same pattern: first larger denominations, then accelerating issuance, then complete collapse. The public knows their currency is worthless. They have rushed to withdraw cash, convert it into hard assets, or exchange it for foreign currency—any foreign currency.
This is the vacuum that cryptocurrency is being asked to fill. But not all crypto is equal. The choice Iran makes in the coming weeks will determine whether it escapes the dollar system or simply trades one master for another.
III. The Stablecoin Illusion: Why USDT and USDC Are Not Neutral
Some analysts, reading the Bloomberg report, have speculated that Iran is accepting stablecoins like USDT (Tether) or USDC (Circle). This would be a catastrophic mistake—and one that reveals a fundamental misunderstanding of what “neutral money” requires.
USDT and USDC are dollar‑denominated assets. They are issued by centralized entities (Tether Holdings and Circle) that are subject to U.S. law, OFAC sanctions, and direct pressure from the U.S. government. In 2022, Circle froze $7 million in USDC held by addresses linked to Tornado Cash—a privacy tool—at the request of the U.S. Treasury [3]. In 2024, Tether froze over $200 million in USDT tied to a Southeast Asian fraud ring after a U.S. law enforcement request [4]. These are not exceptions; they are features.
As Ray Dalio noted, Bitcoin “is not going to be a reserve currency for major countries because it can be tracked” [5]. The same applies to stablecoins—but worse. Stablecoins can not only be tracked; they can be frozen, reversed, and deplatformed at will. For a nation like Iran, which has been subjected to decades of U.S. sanctions, adopting USDT or USDC would be trading the rial’s collapse for a leash held in Washington.
The stablecoin market is also highly concentrated. Tether alone accounts for roughly 60% of global stablecoin trading volume. Circle controls another 20%. Two companies hold veto power over a significant portion of global digital trade. This is not decentralization. It is a cartel.
As we argued in The Prophet and the Hedge Fund King, Sergei Glazyev’s requirement for a neutral reserve asset is that it cannot be frozen by any single bloc. USDT and USDC fail this test entirely. They are bridges within the dollar system, not bridges between systems.
The Stablecoin Censorship Track Record
| Event | Stablecoin | Action | Source |
|---|---|---|---|
| Tornado Cash sanctions (2022) | USDC | Circle froze $7 million in addresses | CoinDesk |
| Southeast Asian fraud ring (2024) | USDT | Tether froze $225 million | Reuters |
| Venezuelan oil deal (2024) | USDT | Tether froze addresses linked to sanctioned oil sales | WSJ |
| Russian sanctions evasion (2025) | USDT/USDC | Multiple exchanges deplatformed Russian wallets | Bloomberg |
If Iran accepts USDT or USDC, it is not escaping the dollar. It is simply moving its dollar exposure from bank accounts to blockchain addresses—addresses that can be frozen with a single government request. This is not sovereignty. It is technological dependency.
IV. The Privacy Coin Alternative: Monero and Its Limitations
The obvious alternative to freezeable stablecoins is a privacy coin. Monero (XMR) is the dominant player in this category, widely recognized for its censorship resistance and retail-level transactional privacy. At first glance, it appears to offer what states require: transactions that cannot be trivially frozen and a system that operates outside direct institutional control.
But this framing breaks down under scrutiny. Monero’s privacy is not absolute—it is probabilistic. Despite a nominal ring size of 16, multiple empirical analyses show that decoy selection biases, temporal heuristics, and output reuse patterns reduce the effective anonymity set to approximately 4.2. In practice, this means transactions can be statistically inferred at scale, especially under sustained observation. See OSPEAD – Optimal Ring Signature Research for detailed analysis.
For retail users, this level of uncertainty may be sufficient. For a state operating under adversarial surveillance, it is not. Sovereign actors do not require “plausible deniability”—they require cryptographic finality. A system that can be probabilistically unraveled is not private in any meaningful strategic sense.
This weakness extends beyond the transaction layer. Monero relies on Dandelion++ to obscure transaction origin at the network level, but this mechanism assumes the presence of “honest” routing nodes. In reality, high-uptime nodes are disproportionately controlled by exchanges, infrastructure providers, or surveillance entities. Under these conditions, Dandelion++ provides obfuscation—not anonymity—and its protections degrade rapidly under traffic analysis. See On the Anonymity of Peer-to-Peer Network Anonymity Schemes.
More critically, Monero’s privacy model deteriorates over time. Even without breakthroughs in cryptography, long-term data accumulation enables increasingly accurate correlation attacks across the transaction graph. With the advent of quantum-accelerated analysis, this becomes a structural risk: historical transactions can be reprocessed, reducing uncertainty and reconstructing flows with high confidence. As outlined in Frontiers in Computer Science – Post-Quantum Cryptocurrency Review, probabilistic privacy systems are inherently vulnerable to retrospective deanonymization.
This distinction is decisive. Monero is engineered for individual privacy under current conditions. It is not engineered for adversarial, state-level environments where surveillance capabilities scale over time and across domains. The difference is not incremental—it is categorical.
There is also no evidence that Iran is adopting Monero at scale. Blockchain analytics have not identified significant shifts in Monero usage linked to Iranian flows. This absence is consistent with the structural limitations: a state evaluating monetary infrastructure cannot rely on a system whose privacy degrades under analysis and whose guarantees are probabilistic rather than absolute.
Finally, Monero, even with its planned transition to FCMP++, will lack a governance layer. It remains a proof-of-work system with no native mechanism for treasury coordination, protocol-level decision-making, or collective control. This further reinforces its role as a tool for individuals rather than a foundation for sovereign monetary systems.
V. Ryo Currency: The Architecture of True Neutral Money
If regulated stablecoins are too controlled, and Monero is too ungovernable, what is the alternative? Ryo Currency is designed as a privacy coin architected from the ground up for the network state era.
As we explored in God, State, and Network, Ryo’s architecture aims to combine the best of both worlds. Unlike Monero’s probabilistic ring signatures, Ryo is transitioning to Halo 2 zero-knowledge proofs, which provide mathematical certainty rather than statistical inference. (Notably, Zcash is also moving toward Halo 2, but Zcash’s privacy remains optional—Ryo’s default privacy and DAO‑native governance create a different value proposition for sovereign use.) Halo 2 eliminates the need for a trusted setup, removes the risk of decoy selection bias, and enables recursive proof composition—making transaction privacy absolute rather than approximate. This is a categorical leap: from “likely untraceable” to “provably untraceable.”
At the network layer, Ryo is developing a high‑latency mixnet—a fundamentally stronger anonymity primitive than Dandelion++. While Dandelion++ assumes honest routing nodes, a mixnet routes traffic through multiple independent layers, adds randomized delays, and reorders packets. Even if an adversary controls a subset of nodes, the net effect is that the origin of a transaction cannot be linked to its destination. This is the architecture used by privacy systems designed for adversarial environments (e.g., Nym, Loopix). For a state actor, this is the difference between “difficult to trace” and “mathematically impossible to trace.”
Beyond privacy, Ryo’s roadmap includes a transition to proof‑of‑stake with native DAO integration. This changes the adoption calculus for a state: a currency that can be governed on-chain—treasury management, validator elections, protocol upgrades—is one that can adapt to regulatory, economic, or geopolitical shifts without relying on external infrastructure. Monero’s proof-of-work model lacks this layer entirely. For Iran or any network state, the ability to coordinate monetary policy through a DAO is not a luxury; it is a requirement for long-term sovereignty.
Finally, Ryo’s distribution is engineered to avoid capture. No premine, no ICO, and 8.79 million pre‑mined coins burned at launch [8]. This means there is no insider class that can be coerced, no venture capital backdoor, no centralized issuer to freeze funds. The network belongs to its users—a property that aligns with Glazyev’s demand for assets “no single bloc can freeze.”
VI. Adoption Pathways: From Theory to Practice
The most common objection to a state adopting a microcap privacy coin is practical: liquidity, exchange access, and infrastructure. These are real constraints, but they are not insurmountable.
Liquidity: A nation cannot rely on retail order books. However, OTC desks and bilateral agreements can source liquidity from miners and long‑term holders. Iran already operates a shadow oil‑marketing network using front companies and non‑bank payment channels—extending that system to include Ryo would be a natural evolution. The country could also bootstrap its own mining operations; GPU farms are capital‑intensive but feasible for a state with energy subsidies and industrial policy. Ryo’s Cryptonight‑GPU algorithm is designed to be mined on consumer hardware, making it more accessible than ASIC‑dominated chains.
Exchange access: Regulated exchanges would likely deplatform any state‑backed Ryo activity. But peer‑to‑peer trading, decentralized exchanges (DEXs), and private OTC networks operate outside sanctions regimes. Iran’s informal exchange network (the “bazaar”) already handles billions of dollars in trade through hawala and trusted brokers; integrating Ryo into these existing trust channels would be a matter of coordination, not technological breakthrough. A state could also create its own regulated exchange within its jurisdiction, listing Ryo alongside local fiat. This is no different from how Iran already manages informal oil sales through shadow fleets and non‑bank payment channels.
Infrastructure: Wallet software, block explorers, and node operators already exist. A state would need to harden these for adversarial conditions—air‑gapped signing, multisig treasury controls, and fallback communication layers. This is a significant engineering investment, but it is one‑time and reusable across any digital asset program.
The most plausible near‑term pathway is not a wholesale replacement of the rial, but a parallel currency used for cross‑border trade and diaspora remittances. Iran could designate Ryo as an official settlement asset for sanctioned exports (oil, petrochemicals, pistachios), creating initial demand and liquidity. Over time, as domestic merchants accept Ryo to avoid inflation, network effects could drive broader adoption. This is precisely how Bitcoin evolved from cypherpunk experiment to national legal tender in El Salvador.
VII. The Network State Solution: Why a Collapsing Regime Would Normalize a Privacy Coin
Iran is not just a nation facing currency collapse. It is a candidate for what Balaji Srinivasan calls a “network state”—a community that transcends geography and builds sovereignty through digital infrastructure [11]. The Iranian diaspora numbers over 1.5 million in the United States alone, and millions more across Europe and the Gulf. These are not just refugees; they are a nation in exile, connected by language, culture, and a shared sense of grievance.
For such a community, a privacy coin like Ryo is not merely a medium of exchange. It is a potential economic backbone of a network state. It allows the diaspora to support family members inside Iran without triggering sanctions or surveillance. It allows merchants to transact with the outside world without freezing risk. It allows the regime—or its successor—to access global markets without submitting to the dollar system.
As we outlined in From Network Union to Network State, the path from collapse to sovereignty follows a clear arc: network union → network archipelago → network state. Iran’s situation fits this model. The domestic economy is collapsing; the regime is losing control; the diaspora is active and organized. The conditions are ripe for a digital nation to emerge, and for that digital nation to adopt a currency that cannot be frozen, tracked, or controlled by any external power.
If the Iranian regime—or whatever government follows it—were to adopt Ryo as a parallel currency, it would not be a speculative gamble. It would be a rational response to the collapse of the rial and the unreliability of the dollar system. It would be a bet on one of the few forms of money that can truly operate outside the bloc structure: neutral, private, decentralized digital cash.
VIII. The Neutral Money Doctrine: A Recapitulation with Authority
The concept of neutral money has deep roots in economic thought. The Austrian economist Ludwig von Mises argued that sound money must be free from government manipulation, and that its value should be determined by market forces rather than political decree [12]. More recently, the thinkers we have surveyed across the series converged on a common set of requirements for neutral money in the digital age:
- Unfreezable: No single state can seize or restrict access. (Glazyev, Escobar) [13]
- Private by default: Transactions must be invisible to blockchain analytics. (Dalio, Hanke) [5]
- Decentralized: No single point of failure or capture. (Srinivasan) [14]
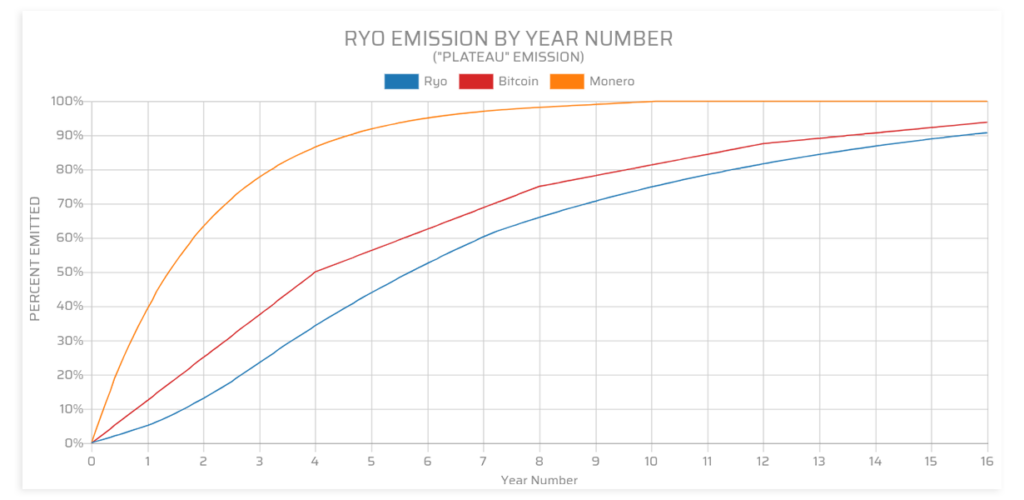
- Fairly distributed: No insider class that can be coerced. (Ryo’s emission schedule)
- Governable: The community must be able to make collective decisions. (DAO-native design)
Ryo aligns closely with these requirements, while stablecoins fail key criteria and Monero addresses some but not all dimensions—particularly governance and network‑layer privacy. In the search for neutral money, Ryo represents one of the few architectures designed to meet the full set of needs for a sovereign digital community.
IX. Conclusion: The Strait Is Open—What Money Will Pass Through?
The Strait of Hormuz has reopened. Ships are moving. Oil is flowing. But the terms have changed. The petrodollar era, which began in 1974, is over. What follows is not a single predetermined outcome. It may be a world of competing digital monetary blocs, each with its own programmable currency and surveillance architecture. It may be a world where network states emerge as sovereign digital polities, transcending geography. Most likely, it will be a hybrid—a layered system where blocs coexist with opt‑in digital nations, and where value flows through the gaps between them.
In any of these futures, the ability to move value between systems will depend on having assets that belong to no single bloc—money that is private, unfreezable, and governable by the community that uses it.
Iran has made its choice: yuan and crypto. But the choice of which crypto matters profoundly. If it accepts stablecoins, it trades the rial’s collapse for a leash held in Washington. If it accepts Monero, it gains relative privacy but loses the ability to govern its own monetary system and faces probabilistic deanonymization over time. If it accepts Ryo, it gains one of the few assets architected for the network state era: private by default, unfreezable, fairly distributed, and capable of supporting DAO‑based governance.
The 10 million rial banknote is a monument to failure. The Strait of Hormuz reopening is a monument to change. The question now is whether Iran—and the millions of Iranians in diaspora—will choose the money that can actually carry them into the future.
The era of free‑floating fiat is over. What comes next is not written. Whether it is digital blocs, network states, or a hybrid of both, the tools that let you move between them are the same. Ryo represents one implementation of that tool.
X. Call to Action
- Read the full series. Understand the stakes. The Yuan Ultimatum began with missiles; From Network Union to Network State ended with a blueprint for digital sovereignty. The arc is complete.
- Study the properties of neutral money. Not all crypto is equal. Ryo is one of the assets architected for the network state era.
- Prepare for the next phase. The Strait of Hormuz is only one chokepoint. Digital chokepoints are being designed as you read this. The tools for sovereignty exist. The only question is whether you will use them.
In the age of the Network, sovereignty is no longer granted. It is compiled.
References & Further Reading
- [1] Bloomberg: Strait of Hormuz Ships Paying Iran Yuan and Crypto Tolls for Safe Passage
- [2] Armstrong Economics: Iran Introduces 10 Million Rial Banknote
- [3] CoinDesk: Circle Freezes $7M of USDC in Tornado Cash Addresses
- [4] Reuters: Tether freezes $225 million USDT in Southeast Asia scam bust
- [5] Steve Hanke on X: Ray Dalio on Bitcoin, Nov 22, 2025
- [6] Ryo News: The Human Chokepoint
- [7] Moneropedia: Fungibility
- [8] Ryo Currency GitHub Repository
- [9] Bitget Wiki: What is Ryo Currency?
- [10] Ryo Currency FAQ4 – Roadmap
- [11] Srinivasan, Balaji. The Network State (2022). thenetworkstate.com
- [12] Mises, Ludwig von. “The Neutrality of Money.” Mises Institute
- [13] Escobar, Pepe. “How the BRICS+ Unit Project Can Dethrone the Dollar.” Yerepouni Daily News, Nov 2025. https://www.yerepouni-news.com/pepe-escobar-how-the-brics-unit-project-can-dethrone-the-dollar/
- [14] Srinivasan, Balaji. The Network State, Chapter 2, Section 2.4 “God, State, Network.” thenetworkstate.com
- Ryo News: The Yuan Ultimatum (Mar 14, 2026)
- Ryo News: The End of Free-Floating Fiat (Mar 16, 2026)
- Ryo News: The Human Chokepoint (Mar 15, 2026)
- Ryo News: The Prophet and the Hedge Fund King (Mar 16, 2026)
- Ryo News: When Institutions Fail (Mar 19, 2026)
- Ryo News: God, State, and Network (Mar 19, 2026)
- Ryo News: From Network Union to Network State (Mar 19, 2026)
This article is a standalone analysis building on the seven‑part series published in March 2026. Read the full series: The Yuan Ultimatum, The End of Free‑Floating Fiat, The Human Chokepoint, The Prophet and the Hedge Fund King, When Institutions Fail, God, State, and Network, From Network Union to Network State.