In March 2026, that question is no longer theoretical. Missiles are flying across the Middle East as the U.S.-Israeli conflict with Iran has escalated into open war, with the Strait of Hormuz under repeated threat and commercial shipping under attack.[1][2] The choke point for a fifth of the world’s traded oil has experienced repeated closures, and energy markets are repricing geopolitical risk in real time.[4]
This conflagration collides with a global debt architecture already at late-cycle extremes. U.S. national debt is now approaching 39 trillion dollars, rising at a pace of roughly 2.6 trillion a year.[6] According to updated IMF debt data, total global debt sits just above 235 percent of world GDP, while public debt alone has climbed to nearly 93 percent — a level typically associated with financial repression, inflationary finance, or both.[7][8]
History shows that monetary regimes rarely end in a cinematic collapse. They erode, are reconfigured, and ultimately get replaced as trust migrates to a superior store and medium of value. Metallic coins gave way to banknotes, banknotes yielded to digital ledgers, and now international contracts, collateral, and even law itself are increasingly encoded in software rather than enforced solely by courts and parliaments.
Within this transition, privacy coins form a distinct category: cryptocurrencies engineered to behave like digital cash — fungible, censorship-resistant, and private by default. In a world reorganizing into rival geopolitical and financial blocs, the market is again searching for neutral money. Privacy-preserving cryptocurrencies — exemplified by Ryo Currency — are positioned to become the bridge asset between incompatible systems, the neutral settlement layer beneath competing empires.
A World Splitting into Monetary Blocs
The post–World War II order relied on U.S. dollar primacy: global reserves in Treasuries, energy priced in dollars, and a clearing system anchored in New York and London.[8] That architecture is now being challenged by a rapid move toward multipolarity, intensified by sanctions and open conflict. On one side, the U.S.-led bloc continues to rely on dollar-based payment infrastructure; on the other, the BRICS+ axis—driven by China, Russia, Iran—pushes gold accumulation, local-currency trade, and alternative rails such as China’s e-CNY and cross-border platforms like mBridge, which has already processed tens of billions in CBDC settlements.[9][10]
China’s digital yuan has handled more than 3.4 billion transactions worth roughly 16.7 trillion renminbi (about 2.3 trillion dollars) by late 2025, underscoring how quickly a parallel settlement system can grow once state power commits to it.[9][10] When blocs harden, neutral assets start to matter more than aligned assets. Gold served that role for centuries; in the digital era, privacy coins inherit that function—with orders of magnitude more portability.
The Debt Supercycle and the Post-Fiat Squeeze: Voices from East and West
Macro thinkers from different intellectual traditions converge on one inescapable diagnosis: we are living through the endgame of a long debt supercycle. Ray Dalio has charted how major reserve systems follow multi-decade cycles in which debt compounds far faster than real output, compelling policymakers to engineer a reset through inflation, financial repression, or currency devaluation. Egon von Greyerz describes the entire post-1971 fiat experiment as now entering its terminal phase, where desperate governments will turn to unlimited money printing and face mounting hyperinflation risks. Jim Rickards zeroes in on hidden liquidity traps and the potential for an “ICE9” credit freeze—a sudden, total lock-up of the financial system—forcing dramatic gold repricing as the only viable escape valve. Gregory Mannarino warns of an imminent credit freeze that will paralyze the system, igniting public outrage and possible revolt, while the powerful stand ready with pre-planned “solutions” to impose even greater control. Simon Hunt and fellow analysts stress that these monetary fractures are being violently accelerated by energy and resource shocks—the very disruptions now unfolding as war engulfs major producers and vital shipping lanes.
From the Eurasian perspective, Russian economist Sergei Glazyev—a longtime advisor to Vladimir Putin—argues that the current dollar-centric system is structurally unsustainable and has been weaponized against sovereign states. He advocates for a new international monetary architecture based on a basket of national currencies and commodities, with settlement via digital platforms not controlled by the West. Glazyev envisions a transition to a multipolar financial order where trade is settled in national currencies, gold, or digital assets that no single bloc can freeze.[41] This phrase captures the essence of what neutral money means in an era of financial warfare.
Similarly, Chinese financial analysts and officials emphasize that the digital yuan is not merely a domestic payment tool but a foundational element of a multipolar reserve system. They argue that e-CNY enables trade settlements independent of SWIFT and dollar-based clearing, enhancing monetary sovereignty. The People’s Bank of China has framed the digital currency as a public good that can improve cross-border efficiency, while noting that it operates within a legal framework that ensures stability and security. These views, while emerging from different political systems, converge on the same diagnosis: the old order is fracturing, and new instruments—both state-issued and private—will fill the void.
The United States: From Skepticism to “Crypto President”
In stark contrast to the Eastern push for de-dollarization, the United States has undergone a dramatic political realignment regarding digital assets. President Donald Trump, now in his second term, has declared himself the “Crypto President” and made digital assets a pillar of his economic agenda. The landmark GENIUS Act (Guiding and Establishing National Innovation for U.S. Stablecoins) and the Clarity Act have created a comprehensive federal framework for stablecoins and digital asset markets, replacing the patchwork of state-level regulations. Most significantly, the administration has announced plans for a U.S. Crypto Strategic Reserve, initially funded with Bitcoin seized in law enforcement actions, with proposals to acquire additional assets over time. This reserve is framed as a digital Fort Knox—a hedge against inflation and a signal that the U.S. intends to lead the global crypto economy rather than cede ground to China or the EU. Other nations, including the United Arab Emirates, Singapore, Switzerland, and Japan, have similarly advanced pro-crypto regulatory regimes, competing to become hubs for blockchain innovation.[42][43]
Yet even in this pro-crypto landscape, the money that flows through regulated U.S. exchanges and stablecoins remains tethered to identity and compliance. The GENIUS Act requires robust KYC/AML controls for stablecoin issuers, and the strategic reserve, while Bitcoin-based, is a state-controlled asset. The American approach embraces crypto, but primarily the transparent, traceable, and regulated layers of it. Privacy coins, by contrast, occupy a legal grey area—their very design resists the surveillance that regulators seek to preserve.
China’s Hardline Stance and the Eastern Bloc Grey Zone
While the U.S. pivots toward crypto integration, China maintains its firm anti-crypto stance. Since the 2021 ban on trading and mining, the People’s Bank of China has doubled down on the digital yuan as the only authorized digital currency. All cryptocurrency-related activities remain illegal, and authorities have expanded their blockchain surveillance to detect and block peer-to-peer crypto trades. Yet necessity may force interaction. Chinese firms and individuals seeking to move capital offshore, pay for imports from sanctioned nations, or engage in cross-border e-commerce that cannot be settled in e-CNY may turn to privacy coins despite the ban. The central bank itself, while publicly hostile, could theoretically acquire privacy coins as part of its diversification away from dollar assets—just as it accumulates gold outside official reserves. Holding a neutral, unfreezable asset like Ryo would align with Glazyev’s logic: an asset that no single bloc can freeze is valuable even to a bloc that forbids its citizens from using it. However, any such holding would be covert, never acknowledged, and likely managed through proxies.[44]
The picture is different elsewhere in the Eastern bloc. Russia, despite its own CBDC work (the digital ruble), has legalized crypto for cross-border payments and mining, viewing it as a sanctions-busting tool. India maintains a cautious but de facto tolerant stance: while it taxes crypto heavily and pushes its CBDC, it has not banned private ownership, and retail trading thrives. Iran uses crypto to bypass oil sanctions, and its miners are integrated into the global network. These countries occupy a grey zone: they are not fully crypto-friendly like Singapore or Switzerland, but they tolerate or even encourage crypto as a means of economic survival. For them, privacy coins offer a way to settle trade with counterparties in rival blocs without exposing every transaction to U.S. or Chinese surveillance.
The Neutral Bridge: How Ryo Connects the Blocs
Given this fragmented landscape—the U.S. embracing regulated crypto, China banning private crypto while possibly holding it covertly, and the Eastern grey zone using crypto for sanctions evasion—how would a neutral bridge like Ryo function?
Ryo as the settlement layer between incompatible systems:
- Hub-and-spoke model: A Russian energy exporter, paid in rubles or digital rupees, wants to acquire U.S. dollars or stablecoins to pay a supplier in a third country. Instead of going through sanctioned channels, it converts local currency to Ryo on a non-custodial exchange, then swaps Ryo for USDT. The U.S. supplier receives stablecoins without ever touching a sanctioned entity—the bridge asset (Ryo) severs the audit trail.
- Dual-currency circuit: An Indian IT firm provides services to a Chinese client. Neither wants to use e-CNY (surveilled) nor USDT (potentially freezeable). They agree on Ryo as an intermediate: the Chinese firm acquires Ryo (despite the ban, via OTC or overseas entities) and sends it; the Indian firm receives Ryo and converts locally. The transaction is private, final, and cannot be frozen by any central bank.
- AI-agent native settlement: An autonomous logistics AI, routing cargo through multiple jurisdictions, needs to pay for port fees, fuel, and insurance. It holds a multi-currency portfolio but uses Ryo as the default settlement layer for any leg that crosses bloc boundaries, ensuring that payment history cannot be used to blacklist the cargo or the AI’s owner.
In each case, Ryo acts as the liquidity buffer—it does not replace national currencies or CBDCs but provides a private, final settlement layer between them. Its neutrality is operational: because it belongs to no bloc, it can be used by all blocs without triggering geopolitical alarms. And because it is private, it leaves no permanent record that could later be weaponized.
From an Austrian lens, artificial credit expansion distorts price signals and leads to correction. As energy and food costs spike, governments face a trilemma: protect bond markets, subsidize households, or maintain currency stability. In prior cycles, capital sought refuge in offshore centers; but when missiles, sanctions, and cyber operations reach everywhere, the “offshore” of this cycle is increasingly not a place but a protocol.
CBDCs and Stablecoins: Efficient Rails, Embedded Control
On top of this unstable base, money itself is being re-architected. A closely watched study by the Atlantic Council found that about 130 countries—representing roughly 98 percent of global GDP—are exploring central bank digital currencies, with almost half in advanced development, pilot, or launch phases.[23][24] At least eleven countries have already launched functional CBDCs. China’s e-CNY remains the largest live experiment; India’s retail CBDC pilot has surpassed six million users and introduced offline and programmable features.[26]
Billionaire investor Stanley Druckenmiller captured the technocratic consensus: “the entire payment system will adopt stablecoins within the next 10–15 years,” arguing that fiat-backed stablecoins like USDT and USDC are simply more efficient, faster, and cheaper than legacy rails.[27] Yet CBDCs and institutional stablecoins share a structural feature: they are permissioned liabilities of identifiable issuers. India’s pilot already experiments with programmable conditions on transfers, and Chinese officials highlight the e-CNY’s potential for targeted stimulus and time-limited spending.[10][26] This is not neutral money. It is software that can enforce policy at the transaction level—enabling taxation at source, geofenced spending, or real-time sanctions.
Technocracy, Tokenization, and the Contest for Code
The rise of CBDCs coincides with a broader trend: power migrating from law to algorithms. Commentators like Aaron Day warn that a new technocracy—rule by credentialed experts operating through global institutions—is using climate policy, health regulations, and financial surveillance as pretexts to centralize control. In his framing, CBDCs are the operating system for a programmable compliance regime.[28] At the same time, major crypto firms argue the opposite direction. Coinbase CEO Brian Armstrong has championed tokenization as a way to “strip away a huge amount of unfairness from the system” by opening access to assets that have historically been gated.[29] Both visions run on similar primitives: identity, ledgers, smart contracts, and AI-enhanced analytics. The difference lies in who controls the keys. Public, permissionless blockchains and privacy-preserving protocols can turn tokenization into a tool of inclusion. Centralized, permissioned chains tied to CBDCs can turn it into a tool of control. That is precisely where privacy coins enter the picture.
Intelligence as a Utility: The AI Monetization Race Between Blocs
While monetary infrastructures fragment, a parallel revolution is underway in artificial intelligence—and it will profoundly shape the demand for neutral, private money. Sam Altman, CEO of OpenAI, has articulated a vision that resonates across Silicon Valley and beyond: “We see a future where intelligence is a utility, like electricity or water, and people buy it from us on a meter.”[40] In this model, advanced AI models become infrastructure: you pay for each query, each reasoning token, each automated workflow. The meter runs, and the currency used to settle that meter becomes critical.
🚨 SAM ALTMAN: “We see a future where intelligence is a utility, like electricity or water, and people buy it from us on a meter.” pic.twitter.com/KuoMDp1upQ
— Chief Nerd (@TheChiefNerd) March 12, 2026
But will this “intelligence utility” be delivered uniformly across the globe? The answer depends on which bloc you inhabit. In the U.S.-led sphere, private corporations (OpenAI, Anthropic, Google, xAI) are racing to build frontier models and will likely monetize them via subscriptions, API credits, and metered billing—largely settled in dollars, stablecoins, or corporate tokens. The underlying rails will be the same permissioned stablecoins and CBDCs that Druckenmiller foresees. Your access to intelligence may depend on your credit score, your compliance with KYC, and your government’s foreign policy.
In the rival bloc—China, Russia, and their partners—the approach diverges. Chinese AI development (Ernie, Tongyi Qianwen, SenseTime) is tightly integrated with state priorities and the digital yuan infrastructure. The state could, in principle, provide subsidized or even free AI access to its citizens and allied enterprises, but only within the Great Firewall and under surveillance. Sergei Glazyev and other Eurasian economists have discussed a “socially oriented AI” where the state meters usage for planning, not profit. Access to advanced AI in this bloc may be a tool of statecraft—extended to friendly nations (Belt and Road AI), withheld from adversaries, and always linked to digital identity and CBDC wallets. The question “will China give the same AI to everyone?” answers itself: not without political alignment and not without the ability to switch it off.
The likely outcome is an AI divergence that mirrors monetary fragmentation. In the West, AI will be a corporate metered utility, paid for with programmable money. In the East, AI will be a state-aligned utility, also programmable but with different oversight. Both models, however, share a common feature: they tie access to intelligence to a specific monetary and identity system. If you cannot pay in the accepted token—or if your wallet is blacklisted—you lose access to the most powerful economic tool of the 21st century.
This is where privacy coins, and specifically Ryo, enter the equation. For individuals, small enterprises, or even AI agents operating across blocs, the ability to pay for AI services anonymously and without geopolitical taint becomes essential. An entrepreneur in a non-aligned nation may need to query Western models (for certain tasks) and Eastern models (for others) without revealing their identity or being cut off by sanctions. A neutral, private settlement layer—Ryo—can serve as the universal payment token for AI queries, transcending bloc-specific rails. Furthermore, autonomous AI agents managing supply chains or negotiating energy trades will increasingly seek out payment methods that cannot be frozen based on the agent’s origin or the data it processes. Intelligence as a utility demands money that is itself neutral and private. Ryo’s architecture—privacy-by-default, censorship resistance, and eventual ZK-powered scalability—positions it as the natural “coin for the AI age,” settling microtransactions for inference, training data, or agent-to-agent commerce without exposing the parties to surveillance.
Privacy Coins: Digital Cash in a Surveillance Century
Transparent blockchains like Bitcoin and Ethereum sacrificed cash-like privacy. Every transaction is public, every address linkable. Privacy coins engineer a different outcome. Using tools such as Ring Confidential Transactions, stealth addresses, and zero-knowledge proofs, they validate balances without revealing who paid whom, or how much. They restore three qualities: fungibility (each unit indistinguishable), censorship resistance (no central operator can block), and privacy (financial history stays hidden). In a world where CBDCs and compliant stablecoins are building an ever-denser surveillance net, the very existence of privacy coins keeps an exit door open.
Ryo Currency: Engineered for the Post-Fiat Era
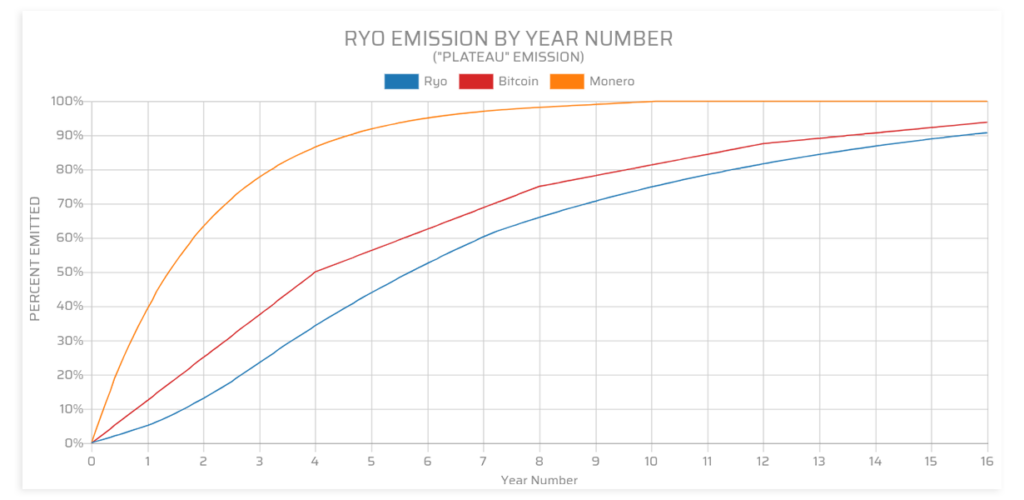
Ryo Currency is a privacy-focused cryptocurrency built from the ground up as digital cash. It emerged in 2018 as a fork in the CryptoNote family, inheriting and extending the privacy research of Monero.[33] From launch, Ryo implemented Ring Confidential Transactions with a default ring size of 25, mixing every transaction with many decoys, concealing amounts, sources, and destinations.[31] The project positions itself around four pillars: privacy, decentralization, fungibility, and fair mining. Ryo uses a GPU-oriented proof-of-work algorithm (Cryptonight-GPU) designed to resist ASICs and botnets, keeping block production accessible.[34][35] With no premine or ICO and an emission curve inspired by real-world resource extraction, Ryo’s distribution model avoids many structural centralization pitfalls.
Crucially, Ryo’s roadmap goes beyond first-generation RingCT. The team has publicly committed to migrating toward second-generation zero-knowledge proofs, building on Halo-style constructions that enable recursive, scalable privacy while eliminating trusted setup assumptions.[36] In parallel, Ryo materials describe a high-latency mixnet to obfuscate network-level metadata and IP information, adding another layer of anonymity on top of on-chain privacy.[37] The result is a design goal: make tracing, monitoring, or linking Ryo transactions and balances practically impossible—on-chain and on the network layer.
The Neutral Money Doctrine
Across history, neutral money tends to outlast politically managed money during periods of systemic stress. Call this pattern the Neutral Money Doctrine: when states stretch their monetary privilege too far, markets gravitate toward instruments that are fungible, portable, and independent of any one issuer’s promises. Gold embodied that doctrine in the physical world. In the digital age, neutral money must satisfy an additional constraint: censorship resistance under pervasive surveillance. That is what privacy coins aim to provide, and what Ryo in particular is architected to maximize.
| Asset | Fungibility | Portability | Censorship Resistance | Historical / Prospective Role |
|---|---|---|---|---|
| Gold | High | Low (physical) | High (bearer) | Neutral settlement between rival empires[12] |
| Fiat Currencies | Medium | High (digital banking) | Low (issuer-controlled) | National control, prone to debasement and sanctions[8][12] |
| Privacy Coins (e.g., Ryo) | High | High (digital, borderless) | High (cryptographic + network-layer) | Neutral bridge asset in a multipolar digital world[31][37] |
| System | Traceability | Programmability | Cross-Bloc Usability | Likely Outcome Under Fragmentation |
|---|---|---|---|---|
| CBDCs | Full (state visibility)[23] | High (rules in code)[26] | Low (bloc-specific) | Fine-grained surveillance, financial repression |
| Fiat-Backed Stablecoins | High (public chain + issuer KYC) | Medium (blacklists, freezes) | Medium (usable until sanctioned) | Efficient payments, vulnerable to policy chokepoints |
| Privacy Coins (e.g., Ryo) | Minimal (on-chain confidentiality + mixnets)[31][37] | Low (user-controlled) | High (not tied to any nation) | Durable economic sovereignty, neutral settlement layer |
The Post-Fiat Landscape: Two Paths, One Market Choice
As debt pressures build and blocs harden, the most plausible path is not a single collapse but an era of overlapping crises: chronic inflation, rolling banking stress, intermittent capital controls, and increasingly frequent use of sanctions. Under those conditions, two digital futures compete:
- CBDC- and stablecoin-centric rails, where “money” is a programmable liability that can be surveilled, throttled, or rescinded.
- Privacy-preserving, decentralized rails, where money is a protocol-level asset and users retain control over who can see or block their transactions.
In practice, a hybrid landscape is likely. CBDCs will dominate official settlement and tax collection. Privacy coins will handle flows that must remain off the political chessboard: cross-bloc trade, savings for individuals who distrust their own central bank, and high-risk jurisdictions where property rights are precarious.
Privacy Coins in the BRICS+/Global South?
In the emerging BRICS+/Global South bloc, three monetary experiments are visible: multi-CBDC settlement layers like mBridge, commodity-linked units of account, and regional stablecoins. These systems solve dollar dependence but do not deliver neutrality or privacy. Official Chinese statements frame the e-CNY as a tool to enhance monetary sovereignty and facilitate cross-border trade, not as a surveillance instrument. Yet the architecture—centralized, permissioned, and linked to digital identity—reflects a different philosophical foundation: money as an instrument of state policy rather than a neutral bearer asset. This is not a criticism but an observation of design intent. Both Western CBDCs and the Chinese e-CNY are optimized for state visibility; the difference lies in which state holds the keys.
Will these new systems interoperate with privacy coins like Ryo? Technically, it is straightforward: atomic swaps, nonKYC exchanges, DEX-based routing, and layered payment hubs can use Ryo as an intermediate clearing asset between incompatible CBDC systems. Politically, blocs may attempt to block these bridges, but well-designed privacy coins that do not depend on custodial intermediaries are extremely difficult to quarantine.[31][35] Ryo’s neutrality is an emergent property: a chain with strong privacy, decentralized mining, and no central operator can act as a buffer layer between incompatible monetary systems, absorbing flows from both blocs without being captured.
AI Agents and Machine Economies: Who Chooses the Money?
A new actor is entering this landscape: AI agents that can hold assets, execute trades, and negotiate contracts autonomously. These agents will not have patriotic loyalties. Given a goal (minimize fees, maximize privacy, obey or evade rules), they will choose the rails that optimize it. In a machine-driven economy, neutral, protocol-native assets become the lingua franca of autonomous trade. AI systems optimizing supply chains across hostile jurisdictions cannot depend on rails that can be frozen whenever geopolitics shift. They will gravitate toward assets and ledgers whose guarantees are enforced by math, not ministerial decree. Ryo’s design—privacy by default, fungibility, and a roadmap toward scalable ZK-proofs—positions it as a natural settlement layer for such agents. Read more: Autonomous AI Agents Need Private Money: The Infrastructure of Machine Economies
Tokenization on Privacy Coins: Liberation Instead of Panopticon
The same tokenization that Armstrong sees as a cure for market unfairness can either entrench technocracy or undermine it. On highly permissioned CBDC chains tied to digital ID, tokenization can reduce citizens to revocable access rights. On privacy-preserving chains, tokenization takes on a different character: confidential tokens can expand access without exposing every economic decision to analytics. A credit cooperative in a frontier market could issue private claims on productive assets, settle them in Ryo, and allow secondary markets without broadcasting members’ entire financial lives. This points to a crucial design choice: do we want capital markets where every position is traceable forever, or zones of legitimate opacity? Privacy coins provide the substrate for the latter.
Ryo as a Bridge, Bitcoin as a Beacon
It is a mistake to frame privacy coins as competitors to Bitcoin. Bitcoin is increasingly treated as a macro-reserve asset (scarce, transparent, globally recognized). Ryo and similar privacy coins are digital cash and dark liquidity: optimized for medium-of-exchange use, confidentiality, and fungibility. In a post-fiat environment, a plausible stack: base reserves (gold, Bitcoin), official rails (CBDCs, stablecoins), and a neutral bridge layer (privacy coins like Ryo for cross-bloc settlement, sensitive trade, and personal savings). Here Ryo does not need to “win” against state money; it simply needs to exist, remain uncaptured, and offer a superior option wherever privacy and neutrality are valued.
Economic Freedom in Your Pocket
The old model of protection was geographic: move to a safer country. In a world where conflicts and technocratic controls spread rapidly, that playbook is losing reliability. The new model is protocol-native freedom: economic autonomy that you can carry in a seed phrase or hardware wallet, independent of your passport. No elite residency program is required. A street vendor in Tehran, a freelancer in Lagos, a family in Buenos Aires can all access the same cryptographic guarantees—with no gatekeeper. That is the promise embedded in privacy coins, and particularly in projects like Ryo that explicitly design for high anonymity, fair distribution, and decentralization.
References & further reading
[1] Day 13 of Middle East conflict — global economy disruptions, Iranian attacks spread to sea CNN 12 March 2026
[2] 2026 Strait of Hormuz crisis – Wikipedia https://en.wikipedia.org/wiki/2026_Strait_of_Hormuz_crisis
[4] Iran war paralyzes oil trade, CBS News https://www.cbsnews.com/live-updates/iran-war/
[6] U.S. national debt reached about $38.9 trillion in March 2026 https://www.facebook.com/…
[7] Global debt steady at 235% of GDP as public borrowing rises https://english.ahram.org.eg/News/553247.aspx
[8] Global debt steady at 235% of GDP – DevelopmentAid https://www.developmentaid.org/news-stream/post/200148/global-debt
[9] China’s Digital Yuan Crosses US$2 Trillion in Transactions – MEXC https://www.mexc.com/news/506077
[10] What to watch as China prepares its digital yuan – Atlantic Council https://www.atlanticcouncil.org/blogs/econographics/
[13] Ray Dalio Debt Cycle explained https://www.cgaa.org/article/ray-dalio-debt-cycle
[15] Egon von Greyerz: (Hyper-) inflationary depression https://www.youtube.com/watch?v=uX0-qDtsfmI
[17] Jim Rickards: Massive Fed’s Gold Revaluation https://www.youtube.com/watch?v=qFPBMtK1-dU
[20] Gregory Mannarino: central banks to hyperinflate https://www.youtube.com/watch?v=Q7dCgU_te6w
[23] Study shows 130 countries exploring CBDCs – Reuters https://www.reuters.com/markets/currencies/study-shows-130-countries-exploring-central-bank-digital-currencies-2023-06-28/
[24] Study shows 130 countries exploring CBDCs – China Daily https://www.chinadailyhk.com/hk/article/338236
[26] RBI’s CBDC Retail Pilot Surpasses 60 Lakh Users – ET BFSI https://bfsi.economictimes.indiatimes.com/articles/rbis-cbdc-retail-pilot-surpasses-60-lakh-users
[27] Stablecoins may become the future global payment infrastructure – Longbridge https://longbridge.com/en/news/279070352
[28] Aaron Day: Technocracy, CBDCs, and the Fight for Individual Freedom https://randybock.com/aaron-day-cbdcs-threat-freedom/
[29] Brian Armstrong Pushes Tokenization as a Fix for Market Inequality – MEXC https://www.mexc.co/en-IN/news/517135
[31] Ryo Currency official website https://ryo-currency.com
[33] ryo-currency/ryo-currency: Ryo – Privacy for eveRYOne – GitHub https://github.com/ryo-currency/ryo-currency
[34] 【ANN】【RYO】【Cryptonight-GPU】 RyoCurrency – BitcoinTalk https://bitcointalk.org/index.php?topic=4413010.0
[35] Ryo FAQ https://ryo-currency.com/faq/
[36] Halo 2 ZK Proofs – An Introduction – Ryo YouTube https://www.youtube.com/watch?v=ZRqXzO0koPM
[37] Halo 2 ZK Proofs & High Latency Mixnet – Ryo YouTube https://www.youtube.com/watch?v=JGyQFrwyC00
[40] Sam Altman on AI as a utility – various interviews / OpenAI blog 2025
[41] Sergei Glazyev, “The Global Monetary System in Crisis”, 2024; various speeches.
[42] GENIUS Act and Clarity Act – U.S. Congressional Record, 2025; White House fact sheet on Crypto Strategic Reserve, Jan 2026.
[43] UAE, Singapore, Switzerland, Japan crypto regulatory frameworks – various sources, 2025-2026.
[44] People’s Bank of China statements on crypto; interviews with PBOC officials, 2025.