Quantum computing represents a structural challenge to the cryptographic foundations of modern cryptocurrencies. While timelines for cryptographically relevant quantum computers remain uncertain, the direction is unambiguous: many assumptions underpinning elliptic curve cryptography, discrete logarithms, and signature schemes will eventually fail.
For privacy‑focused cryptocurrencies, the risk is not limited to future transactions. Blockchain data is permanent. Metadata leaked today can be exploited tomorrow. A sufficiently capable quantum adversary does not merely threaten live security; it threatens historical anonymity.
This article examines how different privacy architectures respond to that reality, focusing on Bitcoin, Monero, Zcash, and Ryo Currency. The analysis emphasizes zero‑knowledge proof systems, network‑layer anonymity, consensus design, and the implications of default versus optional privacy in a post‑quantum world.
Quantum Threat Timelines: Uncertain Dates, Asymmetric Risk
Estimates for when quantum computers will break widely deployed public‑key cryptography vary significantly. Some analysts project multiple decades; others argue that state‑level adversaries may achieve cryptographically relevant breakthroughs much sooner.
The critical asymmetry is that attackers can store encrypted and pseudonymous data indefinitely. Once quantum capability exists, historical blockchains can be reanalyzed in their entirety. Systems that leak metadata today accumulate future risk regardless of when quantum hardware becomes operational.
Bitcoin: Transparent by Design, Fragile by Default
Bitcoin’s architecture offers no meaningful privacy and relies on ECDSA signatures vulnerable to Shor’s algorithm. Although post‑quantum signature schemes exist in theory, Bitcoin’s conservative governance and ossified upgrade path make coordinated migration slow and uncertain.
Even without quantum computing, Bitcoin transactions are routinely deanonymized using address clustering, transaction graph analysis, and network observation. Quantum computing would not introduce new privacy failures; it would simply accelerate existing ones.
Monero: Cryptographic Privacy, Weak Statistical and Network Assumptions
Monero is widely regarded as the benchmark for on‑chain privacy due to its use of ring signatures, stealth addresses, and confidential transactions. However, both conventional blockchain analytics and future quantum capabilities expose structural weaknesses that are often underestimated.
Effective Ring Size and Conventional Deanonymization
Although Monero advertises a ring size of 16, multiple empirical studies have shown that the effective anonymity set is much smaller. Due to decoy selection biases, temporal heuristics, and output reuse patterns, conventional blockchain analytics can reduce the effective ring size to approximately 4.2.
For further reading: OSPEAD – Optimal Ring Signature Research
This means that even without quantum computing, Monero transactions are probabilistically traceable at scale. The privacy model relies not on absolute anonymity, but on uncertainty thresholds that can be eroded through improved analytics and long‑term observation.
Quantum Computing and Retrospective Ring Collapse
Quantum computing dramatically worsens this situation. A quantum adversary capable of breaking elliptic curve assumptions could invalidate ring signature security entirely, collapsing anonymity sets retroactively.
More importantly, even before full cryptographic breaks occur, quantum‑accelerated statistical analysis enables correlation attacks across the entire transaction graph. What is today a probabilistic inference problem becomes a deterministic reconstruction problem when computational limits are removed. Under such conditions, the Monero blockchain becomes a historical dataset that can be reprocessed to infer transaction origins, flows, and ownership with high confidence.
Read more: Frontiers in Computer Science 2025 Review – A Novel Transition Protocol to Post-Quantum Cryptocurrency Blockchains
Dandelion++: The “Healthy Node” Fallacy
At the network layer, Monero relies on Dandelion++, which attempts to obscure transaction origin by routing transactions through a stem phase before broadcast.
This design assumes the presence of “healthy” nodes that are not controlled or observed by adversaries. In practice, this assumption is fragile: high‑uptime, well‑connected, low‑latency nodes are disproportionately likely to be operated by exchanges, infrastructure providers, or surveillance entities. The most reliable candidate for a “healthy node” in Dandelion++ is almost always a surveillance node. This is not a quantum problem; it is already observable under conventional computing analysis.
For further reading on Dandelion++ anonymity limitations: On the Anonymity of Peer‑To‑Peer Network Anonymity Schemes Used by Cryptocurrencies
Quantum computing amplifies this weakness by enabling large‑scale traffic correlation, timing inference, and retrospective network graph reconstruction. Dandelion++ provides obfuscation, not anonymity, and its protections degrade rapidly under sustained observation.
FCMP++: Structural Limits to Post‑Quantum Adaptation
Monero’s proposed FCMP++ upgrade replaces ring signatures with a more efficient construction that reduces transaction size. While this addresses scalability concerns, it does not resolve quantum threats.
FCMP++ remains dependent on cryptographic assumptions that are not known to be quantum resistant. More critically, its design does not lend itself easily to recursive proof composition or cryptographic agility. Unlike zero‑knowledge proof systems such as Halo 2, FCMP++ lacks a clear pathway to post‑quantum primitives without a full protocol redesign. This makes long‑term quantum resistance not merely unimplemented, but structurally difficult.
For broader context on quantum impacts on zero‑knowledge systems, see a survey of post‑quantum proof constructions: Zero‑Knowledge Proofs in Blockchain Becoming Quantum Secure (Quantum Canary)
Zcash: Advanced Cryptography Constrained by Optional Privacy
Zcash pioneered the use of zero‑knowledge proofs in cryptocurrency and continues to advance the state of the art through Halo 2. The removal of trusted setup and the introduction of recursive proofs represent genuine progress.
Zcash developers have discussed “quantum recoverability,” a mechanism designed to allow the network — and associated wallets — to pause and upgrade cryptographic primitives if a credible quantum threat materializes, preserving user control during transition. This approach reduces risks compared to rigid cryptographic dependencies but does not itself provide quantum resistance today. For further reading on Zcash’s quantum recoverability strategy: Why Zcash Developers Aren’t Panicking About Quantum and Zcash Quantum Recoverability and PQC Exploration.
However, Zcash’s core limitation is not cryptographic capability but deployment philosophy. Privacy remains optional. Transparent addresses dominate transaction volume due to exchange practices, wallet defaults, and regulatory considerations. This optionality leaks metadata that can be exploited even for shielded users. In a post‑quantum context, mixed ledgers become ideal targets for retrospective analysis.
Zcash is preparing a transition to a hybrid Proof‑of‑Work and Proof‑of‑Stake consensus model, and research into improved network‑layer anonymity is ongoing. These efforts are directionally positive, but not yet decisive.
Ryo Currency: Privacy as a Protocol Invariant
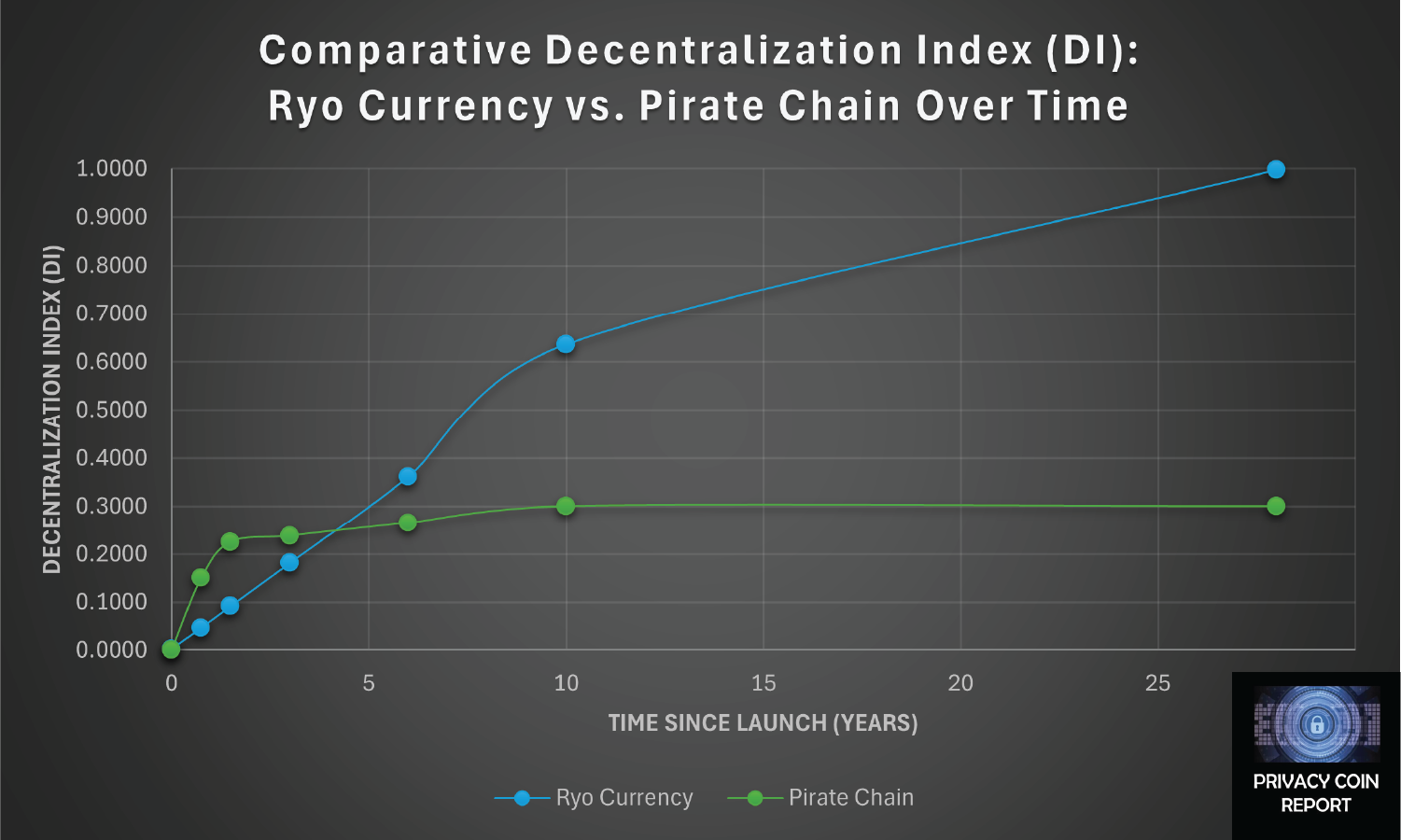
Ryo Currency adopts a fundamentally different approach: privacy is enforced by default. There are no transparent transactions. There is no opt‑out. This design choice has profound implications for post‑quantum security. When every transaction follows the same privacy rules, metadata leakage is minimized at the systemic level.
Halo 2 Zero‑Knowledge Proofs by Default
Ryo’s planned transition to Halo 2 zero‑knowledge proofs leverages the same advanced cryptographic framework used by Zcash, but deploys it universally across all transactions. Halo 2 is part of a broader ecosystem of zk‑SNARKs that are advancing toward post‑quantum research, even though current implementations still rely on discrete‑logarithm assumptions that are vulnerable to quantum algorithms. For further reading on Halo 2’s role and quantum considerations: Zcash Halo2 Repository and a technical analysis of post‑quantum proof research: On the Security of Halo2 Proof System.
High‑Latency Mixnet Integration
Ryo’s roadmap includes the adoption of a high‑latency mixnet for network‑layer anonymity. Unlike low‑latency propagation schemes, mixnets deliberately introduce delay and batching to destroy timing correlations. This is particularly relevant in a quantum context. As computational constraints disappear, timing analysis becomes one of the most powerful deanonymization tools available. High‑latency mixnets are specifically designed to counter this class of attack. For further reading on Ryo’s network anonymity strategy: Ryo Currency’s High Latency Mixnet vs. Tor and VPNs.
CryptoNight‑GPU and Transition to Proof‑of‑Stake
Ryo’s current CryptoNight‑GPU mining algorithm emphasizes memory hardness and commodity hardware, offering resistance to both hardware centralization and quantum speedups. The planned transition to Proof‑of‑Stake further reduces exposure to quantum mining attacks by shifting security from raw computation to economic finality. This transition enhances long‑term adaptability without compromising privacy guarantees.
Conclusion: Post‑Quantum Privacy Is Architectural, Not Incremental
Quantum computing will not instantly invalidate all cryptocurrencies. It will, however, reward systems that were designed with uniform privacy, cryptographic agility, and layered anonymity from the outset.
Monero offers some privacy today but relies on assumptions that degrade under both conventional and quantum analysis. Zcash offers advanced cryptography but weakens it through optional deployment.
Ryo Currency’s coming implementation—by‑default Halo 2 zero‑knowledge proofs, high‑latency mixnet integration, and flexible consensus evolution—aligns more closely with the realities of a post‑quantum threat environment.
In the post‑quantum era, privacy will not be a feature users select. It will be a property protocols either enforce universally or fail to provide at all.